Apple just rolled out a new webpage dubbed “Families” with tips on managing your children’s iPhone and iPad use. The page has a lot of useful information and feels like a response to public concern about smartphone addiction.
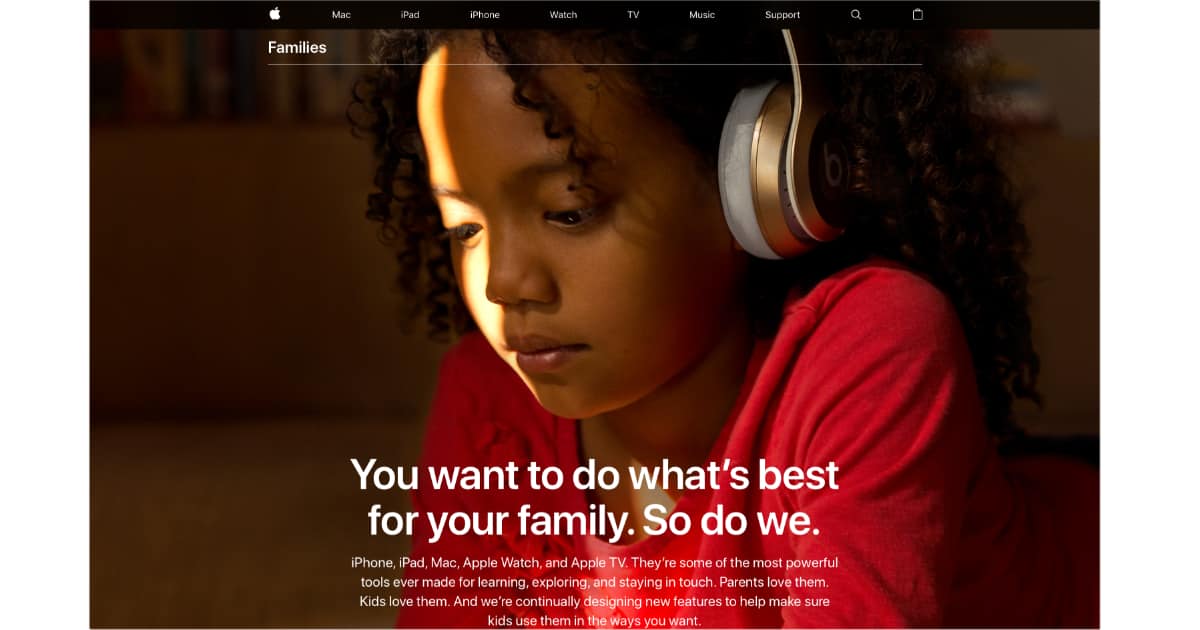
The page includes tips about the kids section on the App Store, managing App Store purchases, using Find My Friends, privacy controls, Emergency SOS, and more. Apple also suggests Apple Watch Series 3 with LTE for your kids so it’s easier to stay in touch in emergency situations.
The Families page comes in the wake of calls from shareholders for Apple to actively address smartphone addiction—something TMO’s John Kheit doesn’t agree with. The Center for Humane Technology called out several companies, too, although the organization pointed to Apple as a company that can help find a solution.
Apple CEO Tim Cook commented on technology addiction in January saying,
I don’t believe in overuse [of technology]. I’m not a person that says we’ve achieved success if you’re using it all the time. I don’t subscribe to that at all.
More robust parental controls are coming to the iPhone and iPad, although Apple hasn’t said how soon that’ll happen. Odds are we’ll see something when iOS 12 is shown off in June at Apple’s annual Worldwide Developer Conference.
I’ve long felt it isn’t Apple’s responsibility to babysit our kid’s online activity, or how they use their Macs, iPhones, and iPads. The new Families webpage seems like a nice way to give parents some ideas on how to better supervise their children’s tech lives, and a part of Apple’s bigger picture with parental controls.



You can find just about anything on the web. You’ve heard it a million times, but for parents, that truism takes on a whole new meaning. In this tutorial, I’ll show you how to protect your family from the wild west of the web, using tools built right in to the Mac.
Apple loves families so much. Just take a look at the child care section on the fancy new Apple campus! Oh wait, there is none.