Yesterday Apple confirmed to The New York Times that a new iOS security feature is coming called USB Restricted Mode. It aims to thwart smartphone forensic attempts to break into an iPhone. But there might already be a workaround.
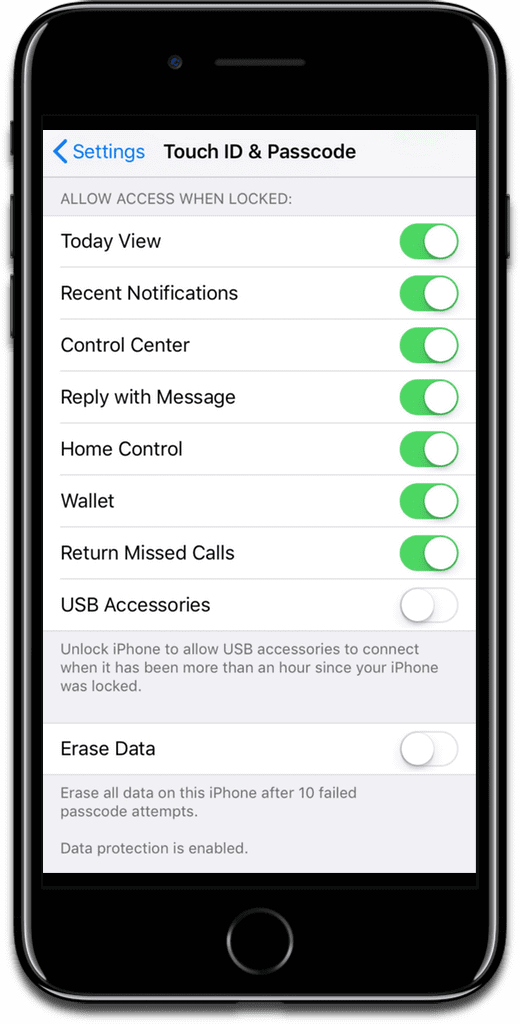
[How to Enable and Disable iPhone and iPad USB Restricted Mode]
GrayKey
A company called Grayshift has frequently been in the news. The company has a device called GrayKey, which hacks into iPhones via the Lightning port. Apple has been planning a security feature that would disable the Lightning port an hour after the iPhone is locked. It can still be charged, but in order to use the port to transfer data a person would need to enter the passcode.
But Motherboard reports that Grayshift is confident that its device is future-proof:
Grayshift has gone to great lengths to future proof their technology and stated that they have already defeated this security feature in the beta build. Additionally, the GrayKey has built in future capabilities that will begin to be leveraged as time goes on.
According to presentation slides from Grayshift, the company has two strategies to work around USB Restricted Mode, called BFU (Before First Unlock) and AFU (After First Unlock). BFU is a “slow brute force” method which means it takes 10 minutes per attempt. This would provide limited data access.
AFU is a “fast brute force” method and supposedly starts when the phone is locked but was turned on and unlocked at some point. This allows for 300,000 cracking attempts and provides “parallel extraction of pre-unlock data.”
Wow this Security Feature of Ios is too good