We are only starting to understand the full extent of the iOS hack revealed Friday by Google researchers. At Wired, Andy Greenberg and Lily Hay Newman argued it changes everything we know about iPhone hacking.
The attack is notable not just for its breadth, but the depth of information it could glean from a victim iPhone. Once installed, it could monitor live location data, or be used to grab photos, contacts, and even passwords and other sensitive information from the iOS Keychain. With such deep system access, the attackers could also potentially read or listen to communications sent through encrypted messaging services, like WhatsApp, iMessage, or Signal. The malware doesn’t break the underlying encryption, but these programs still decrypt data on the sender and receiver’s devices. Attackers may have even grabbed access tokens that can be used to log into services like social media and communication accounts. Reed says that victim iPhone users would probably have had no indication that their devices were infected
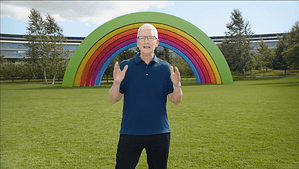
Check It Out: Latest iOS Hack is a Game Changer




I hope all the Apple clones out there that love to trash Google say a big thank-you to them for pointing out this exploit. Can you imagine how many haven’t been found? This only highlights the fact Apple hardware/software is no more safe than any PC or indeed anything connected.
Just saw 60 Minutes and that disgusting Israel Pegasus software that basically makes a joke of anybody connected – or not. I just think Privacy is a joke – a fallacy – Orwell predicted Big Brother but he failed to say a bunch of clones born and babysat on commercial programmed TV wouldn’t even care and indeed welcome being a part of the bitstream on their CONNECTED toy phones and other boxes. Hilarious. ?
“Google hasn’t named the websites that served as a “watering hole” infection mechanism, or shared other details about the attackers ”
Why not
How was this done? Did one simply need to visit the malicious websites?