Chrome, Firefox, Safari, and Tor are vulnerable to a type of cross-browser tracking that can identify users.
Cross-Browser Tracking
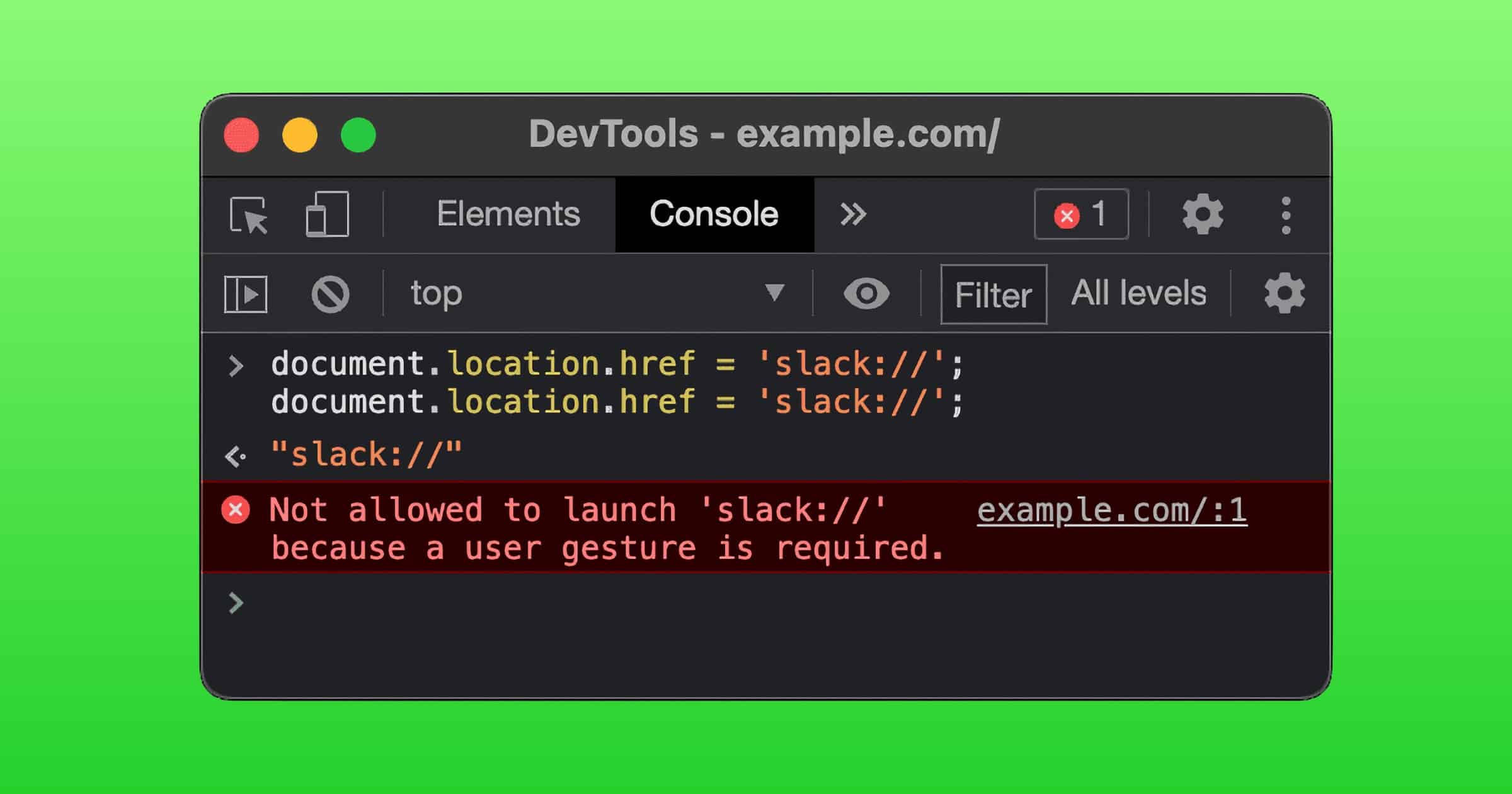
FingerprintJS discovered this vulnerability, called scheme flooding. It uses custom URL schemes as an attack vector. It can collect information about the apps you have installed on your desktop to give you a permanent, unique identifier that can track you across browsers even if you use a VPN or incognito mode.
Additionally, the scheme flood vulnerability allows for targeted advertisement and user profiling without user consent. The list of installed applications on your device can reveal a lot about your occupation, habits, and age. For example, if a Python IDE or a PostgreSQL server is installed on your computer, you are very likely to be a backend developer.
The group says this vulnerability has existed for over 5 years but didn’t find any malicious actors making use of it. They created a demo website, shared the source code on GitHub, and notified all public browser makers.
Yes, this may be annoying or even dangerous.
Yet, I myself prefer targeted ads to those promoting things I’m not at all interested in. Like pet food when I don’t have pets. Instead, make me an offer for a tamagotchi to live in my Mac. 😉