An iPhone zero day has been found in the wild that takes advantage of two vulnerabilities in the Mail app. ZecOps believes at least one nation-state bought the exploit and is using it against a variety of high-profile targets.
Key Takeaways
- These vulnerabilities have existed since at least iOS 6 with the iPhone 5. All iOS versions are vulnerable, including the latest iOS 13.4.1 update.
- They were detected as far back as January 2018.
- Apple says there are patches in the newest iOS 13 beta and will make its way to a public iOS release in the near future.
- The exploit can be used remotely by an attacker sending emails that use a large amount of the device’s RAM.
Details
In iOS 12, a specially-crafted email triggers a vulnerability using iOS MobileMail. On iOS 13 it uses the maild process. One of the vulnerabilities is a zero-click, meaning that it doesn’t require any user interaction.
The researchers investigated a number of their customers’ iPhones in 2019 after they experienced weird crashes with the default Mail app in iOS. They found that although the victim devices successfully received and downloaded the malicious emails, they weren’t found on the mail server, meaning they were deleted by the attackers to cover their trail.
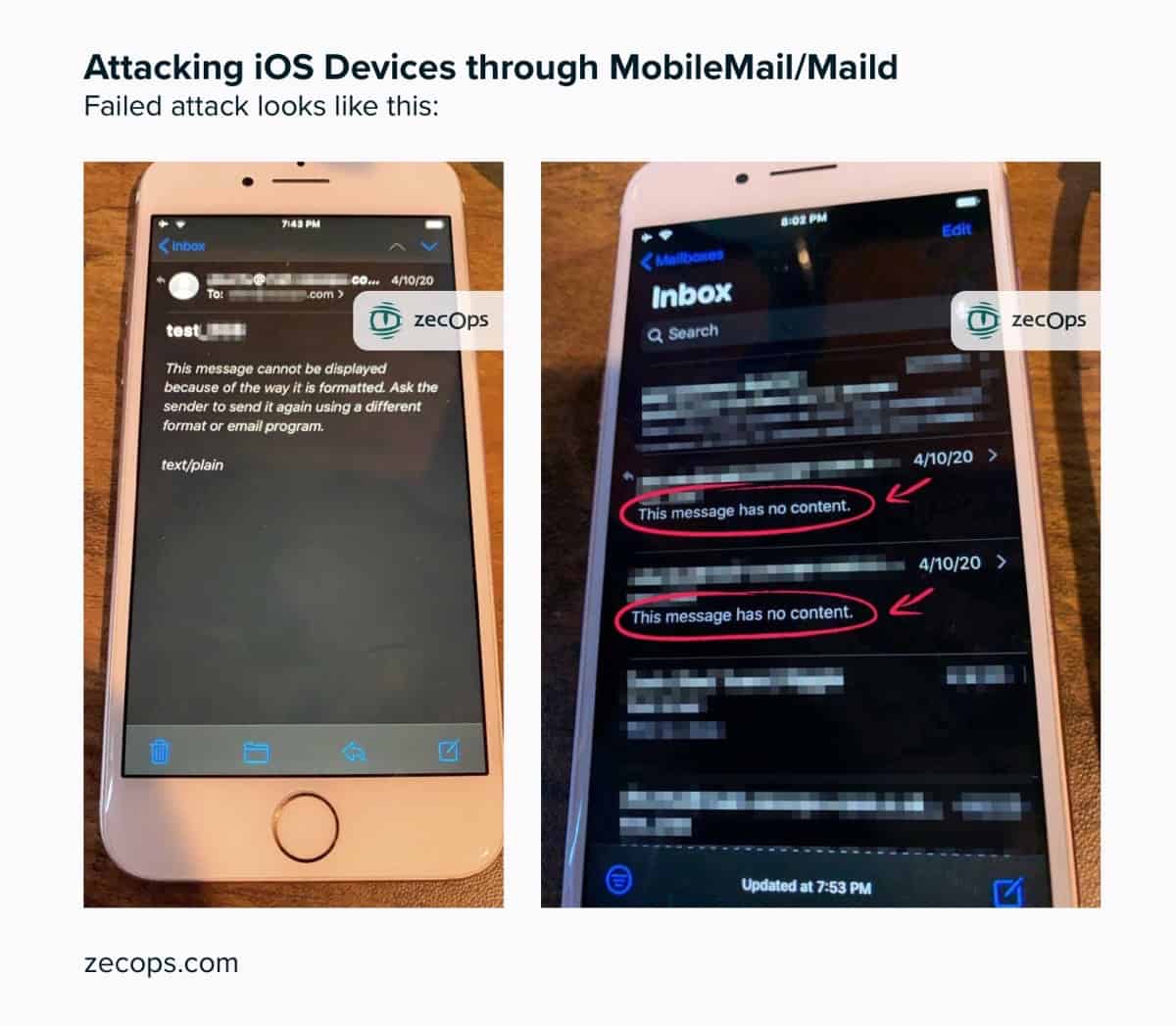
Whether the attack was successful or unsuccessful, the victim would notice the Mail app crashing on iOS 12. On iOS 13, a victim wouldn’t notice anything except for a temporary slowdown of Mail. If the attack failed, the malicious email would display the following message:
This message cannot be displayed because of the way it is formatted. Ask the sender to send it again using a different format or email program.
Further details can be found in the report.
Further Reading
[iPhone Factories in China Cut Workers Due to Drop in Demand]
[Pixelmator 2.5 Adds File Browser, Photo Browser, Image Size Presets]




