There’s new Mac malware in the wild aimed at users who may be a bit less savvy on the nerd scale. Discovered by Malwarebytes (via 9to5Mac), this malware uses interface shenanigans to trick users into permitting other malware to be installed.
Here’s the Skinny
There’s a company called PCVARK that Malwarebytes said “plays dirty.” One of its apps is called Advanced Mac Cleaner (I won’t provide links to it). The installer from that app’s website sneaks in an innocuously named trojan called Mac File Opener, and that’s where it gets tricky.
Thomas Reed of Malwarebytes said:
Once I had installed it and was poking around to see whether it had installed anything new – perhaps a shiny new piece of adware, for example – I discovered an odd app, named Mac File Opener, tucked away where the average user would never see it.
Even more intriguing, this app didn’t have any apparent mechanism for being launched. It hadn’t been added to my login items. There wasn’t a new launch agent or daemon designed to load it. It simply seemed to be sitting there, doing nothing.
Inside Mac File Opener’s info.plist file, however, he found a list of some 232 file types Mac File Opener claims it can open. If you open one of those files types, chances are Mac File Opener gets launched. It then presents users with this dialog:
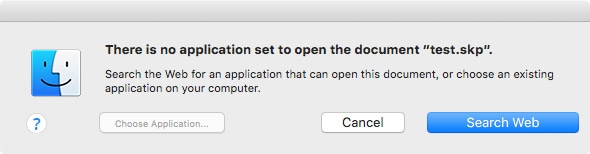
Looks mostly right, but compare it to a legit dialog generated by OS X:
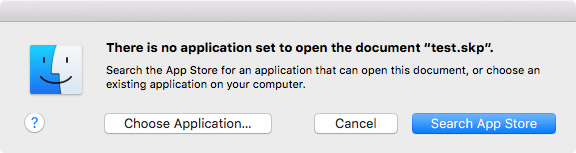
There are a lot of folks who would be lulled into complacency by that first malicious dialog. If the user clicks “Search Web,” he or she is taken to a page at for “Mac File Opener” that tries to convince users to install additional malware. Malwarebytes has the details on that.
So Say We All
The bottom line, though, is don’t install software from websites unless you know precisely what you are doing. This is a point we should help our friends and relatives understand. In my opinion, most users should stick the Mac App Store, despite its warts and shortcomings.
One last note: all of the apps mentioned in this piece are signed with legit (for now) certificates issued by Apple. Malwarebytes considers the apps malware, but because they have a legit certificate, your Mac will install them if you give it permission to do so.