Newly discovered macOS malware targets browsers and crypto wallets, distributed through pirated software. Stay informed and protect your data!
Malware
Fix "macOS Cannot Verify That This App is Free from Malware" [2024]
Getting a macOS cannot verify that this app is free from malware message? Find out two ways to bypass the Mac warning.
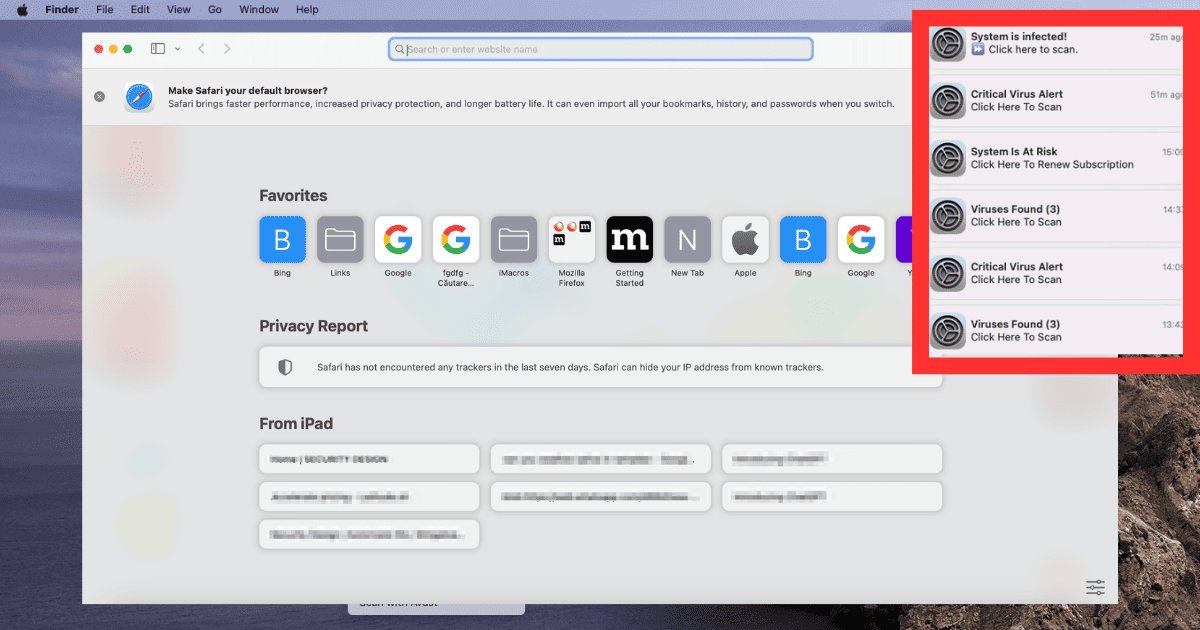
How To Get Rid of "Mac OS: The System Is In Danger" Fake Alerts
Learn how to protect your Mac from the “Mac OS: The System Is In Danger” fake alert scam by removing adware, and securing your browser.
How to Get Rid of aceonaillike.com Notifications on Mac
If you’re being troubled by its push notifications, here’s how to get rid of the aceonaillike.com notifications on your Mac.
5 Best Antivirus Solutions for Mac, iPad, and iPhone
If you’re looking to protect your Mac from viruses, check our round-up of the 5 best antivirus solutions for Mac, iPhone, and iPad.
5 Best Antivirus Tools for MacBook Pro 2024
Still looking for the best antivirus software for your Mac? Arnold Zafra rounds up the five best antivirus for MacBook Pro 2023.
How to Remove Adware From Your Mac and Stay Protected
If you’re being bothered by unwanted pop-ads when browsing the web, learn how to remove adware from your Mac and stay protected.
How to Bypass App Will Damage Your Computer Warning on Mac
If you find yourself getting a [App] Will Damage Your Computer warning on Mac, there’s some things you can do, though proceed with caution.
What is Juice Jacking and How Can You Avoid It on Your iPhone?
Find out more about juice jacking, how it works, and how to avoid it if you need to charge your iPhone in public charging stations.
How to Remove Search Marquis from Your Mac
If your search engine has been replaced with something dubious, you may have Search Marquis malware: here’s how to remove it on Mac.
Bug in macOS Ventura May Have Silently Broken Your Malware Protection; Here’s How to Fix It
Your anti malware tools may be suffering a macOS Ventura bug that breaks them. Here’s how to fix it, until Apple offers a permanent solution.
Apple Makes Anti-Malware Tools for Mac More Proactive
Apple has implemented dramatic changes in its anti-malware tools XProtect and MRT, bringing improvements to Macs’ malware detection feature.
[U: Play It Again, Sam] Update Zoom On Your Mac Now: Vulnerability Could Give Attacker Full Access to Your Computer
An urgent update to the Zoom client for your Mac addresses a serious vulnerability. Install it now to keep your Mac free of malware.
Newly Discovered CloudMensis Malware Attacking Compromised Macs
Reports from cyber security firm ESET indicate that a new malware known as CloudMensis is attacking Macs by utilizing cloud storage services.
Method Found to Run Malware on iPhone Even When It’s Turned Off
Researchers have discovered a way to run malware on an iPhone even when it’s turned off. It takes advantage of Bluetooth, NFC, and UWB chips.
New Malware Known as GIMMICK Affecting Mac Systems in Asia
Volexity’s security experts recently detected new malware, GIMMICK. It’s primarily affecting users in Asia, and there are ways to combat it.
New Malware Coming Through Email Posing as IRS
A new phishing scam posing at the IRS is making the rounds through email. Infamous botnet Emotet is behind many of the attacks.
Scammers Are Using Apple TestFlight and Web Clips To Distribute Malicious Apps to iPhones
A new report said that CryptoRom Bitcoin swindlers are using two new ways to fool users to install malicious apps on iPhones.
Here's What We Know About PYSA Ransomware
PYSA ransomware is a piece of malware from an unknown APT group. It attacks what the FBI calls “soft targets.”
Cybercrime Group 'Sandworm' Uses New Cyclops Blink Malware
A group or individual known as Sandworm or Voodoo Bear is using a piece of malware never before seen in the wild, called Cyclops Blink.
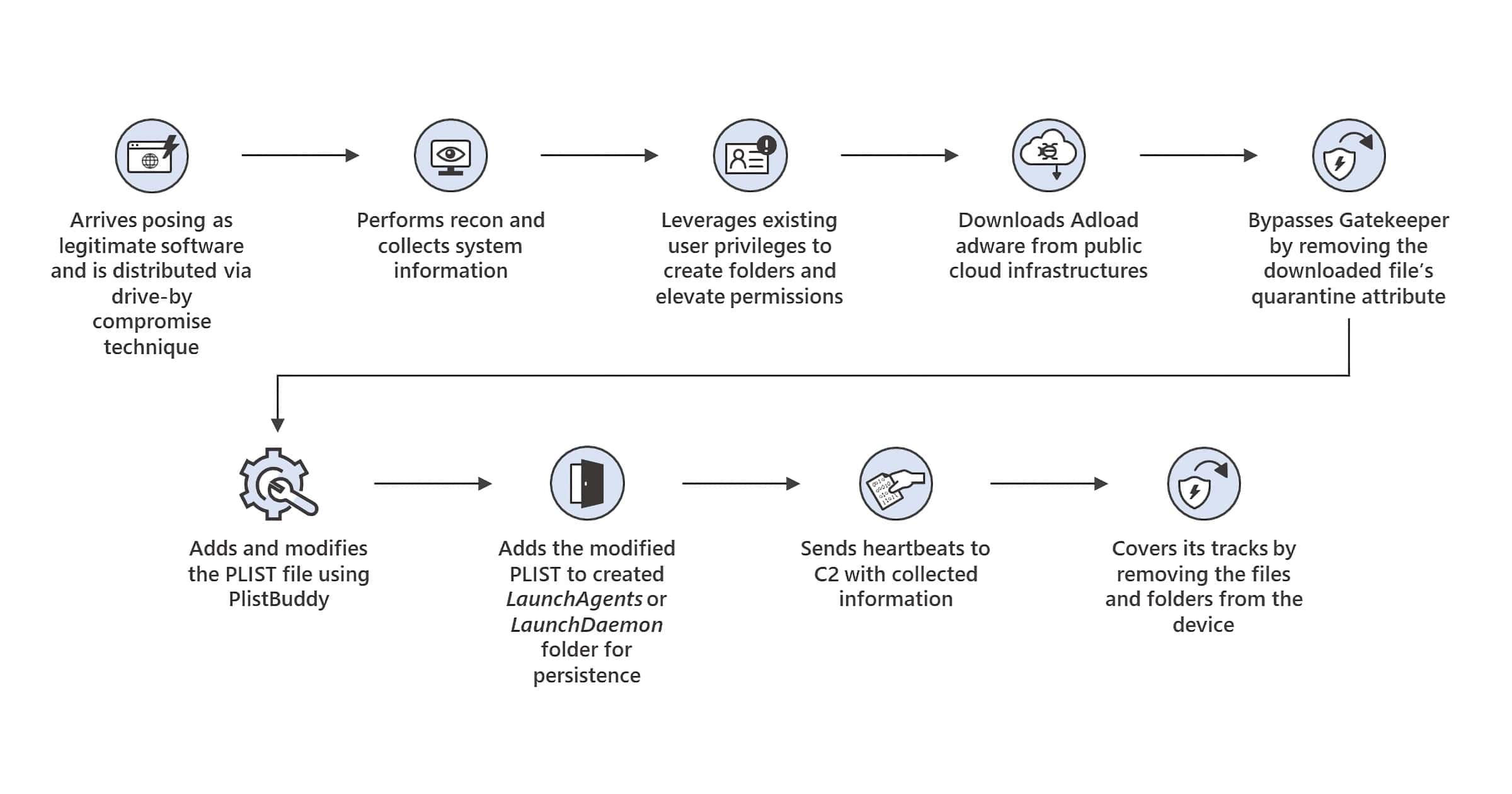
'UpdateAgent' Mac Trojan Can Steal Data and Inject Adware
UpdateAgent is the name of a Mac trojan that Microsoft has been tracking since October, although it first appeared in September 2020.
'OSX.DazzleSpy' is a Fully-Featured macOS Implant for Espionage
OSX.DazzleSpy is a new macOS implant targeting Hong Kong pro-democracy websites. It affects the Safari browser on macOS.
'AccessPress' Themes and Plugins for WordPress Contains Backdoor
JetPack discovered a backdoor found within AccessPress themes and plugins. Every theme and most plugins contain this malware.
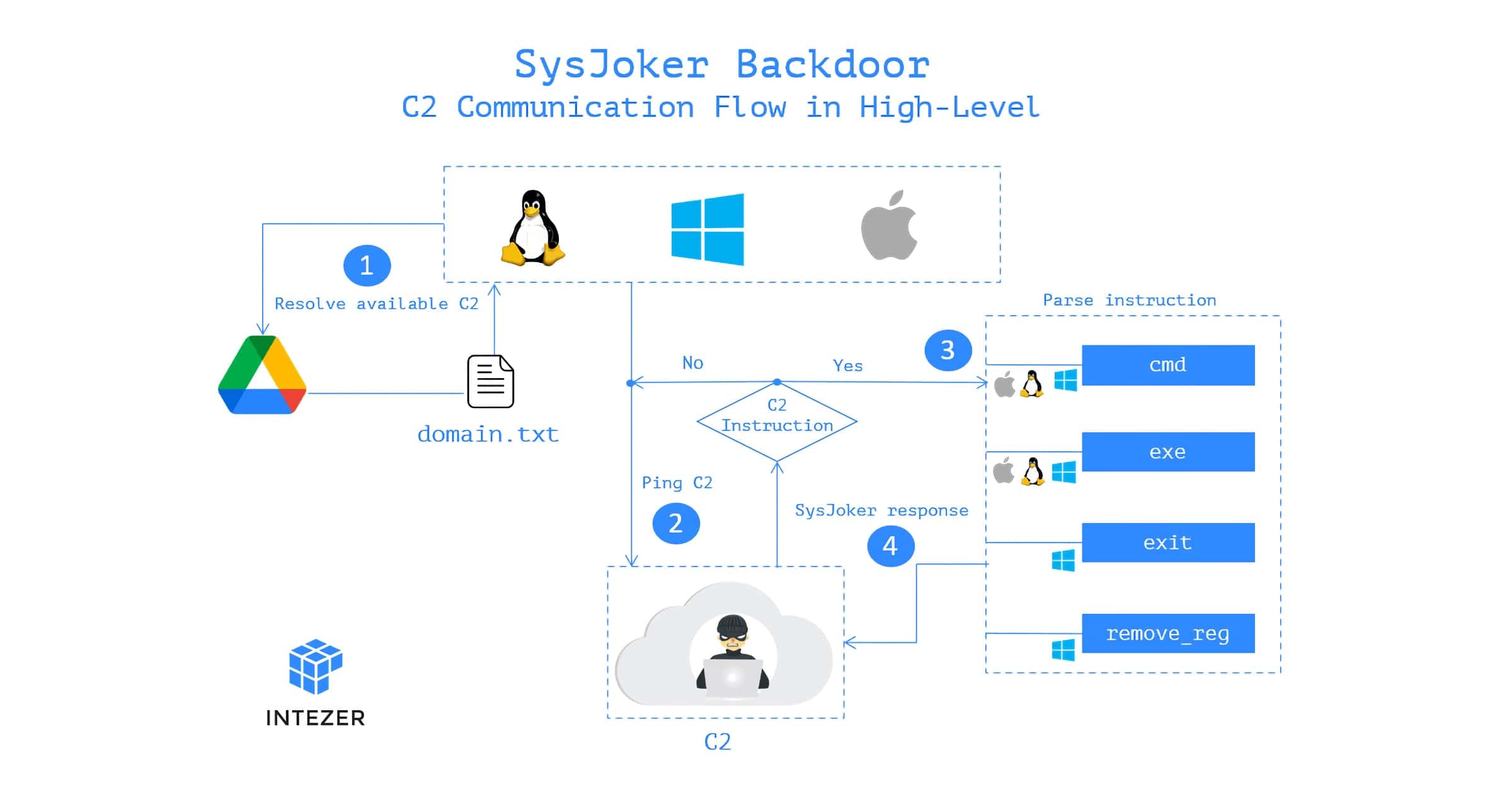
New 'SysJoker' Backdoor is a Multi-Platform Threat for macOS, Windows, Linux
There is a new piece of malware floating around. This SysJoker backdoor was discovered in December 2021 by the Intezer team.

![Fix “macOS Cannot Verify That This App is Free from Malware” [2024]](https://www.macobserver.com/wp-content/uploads/2023/02/Fixing-macOS-Cannot-Verify-That-This-App-is-Free-from-Malware.jpg)









![[U: Play It Again, Sam] Update Zoom On Your Mac Now: Vulnerability Could Give Attacker Full Access to Your Computer](https://www.macobserver.com/wp-content/uploads/2022/08/zoom-update-vulnerability.jpg)