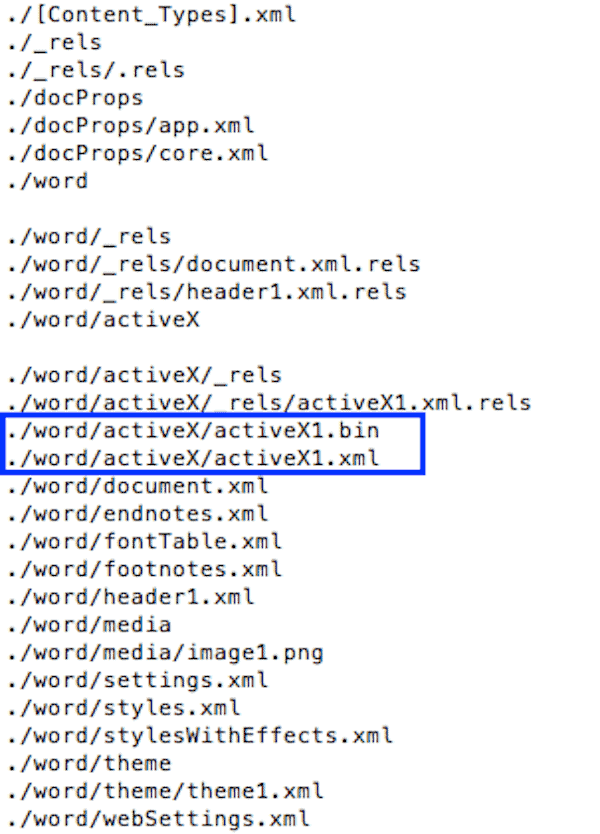
Russian antivirus firm Kaspersky Lab spotted an Adobe Flash bug in the wild. It’s a zero-day exploit used by a group called BlackOasis, and it delivers its payload by way of a Microsoft Word document. The payload in question is FinSpy, a type of surveillance software used by repressive governments and law enforcement.
BlackOasis Adobe Flash Exploit
Anton Ivanov, lead malware analyst at Kaspersky Lab, says:
The attack using the recently discovered zero-day exploit is the third time this year we have seen FinSpy distribution through exploits to zero-days. Previously, actors deploying this malware abused critical issues in Microsoft Word and Adobe products. We believe the number of attacks relying on FinSpy software, supported by zero day exploits such as the one described here, will continue to grow.
Once the zero-day is taken advantage of, FinSpy (also known as FinFisher) is installed on the system. It’s equipped with anti-analysis techniques designed to thwart detection by forensic analysis. After installation, it connects with its command and control (C2) servers which are located in Switzerland, Bulgaria, and the Netherlands. It then waits for further commands.
Kaspersky is “highly confident” that BlackOasis was responsible for previous exploit CVE-2017-8759. BlackOasis uses the same C2 servers for both bugs. Kaspersky thinks that BlackOasis seems to be interested in Middle Eastern politics, United Nations officials, and certain activists and journalists.
Victims have so far been found in Russia, Iraq, Afghanistan, Nigeria, Libya, Jordan, Tunisia, Saudi Arabia, Iran, the Netherlands, Bahrain, United Kingdom and Angola.
Affected Versions
As of yesterday, Adobe has already identified the bug (CVE-2017-11292) and released a security patch for Windows, macOS, Linux, and Chrome OS. Affected versions include:
| Product | Version | Platform |
| Adobe Flash Player Desktop Runtime | 27.0.0.159 | Windows, Macintosh |
| Adobe Flash Player for Google Chrome | 27.0.0.159 | Windows, Macintosh, Linux and Chrome OS |
| Adobe Flash Player for Microsoft Edge and Internet Explorer 11 | 27.0.0.130 | Windows 10 and 8.1 |
| Adobe Flash Player Desktop Runtime | 27.0.0.159 | Linux |
Adobe Flash is insecure and is on its way out. If you’re still using it on your system, be sure to get the latest update for the security patch.
Do ya trust that source?
6/10 😉