Google’s security arm called Project Zero has found a macOS kernel flaw rated “high security” (via AppleInsider).
[German Researcher Gives Apple Details of Mojave Keychain Flaw, Despite no Bug Bounty]
Kernel Flaw
A kernel is the core of an operating system. It has complete control over everything and handles stuff like input/output from software, memory, computer accessories, and more. XNU is the name of the kernel and is used with all of Apple’s operating systems.
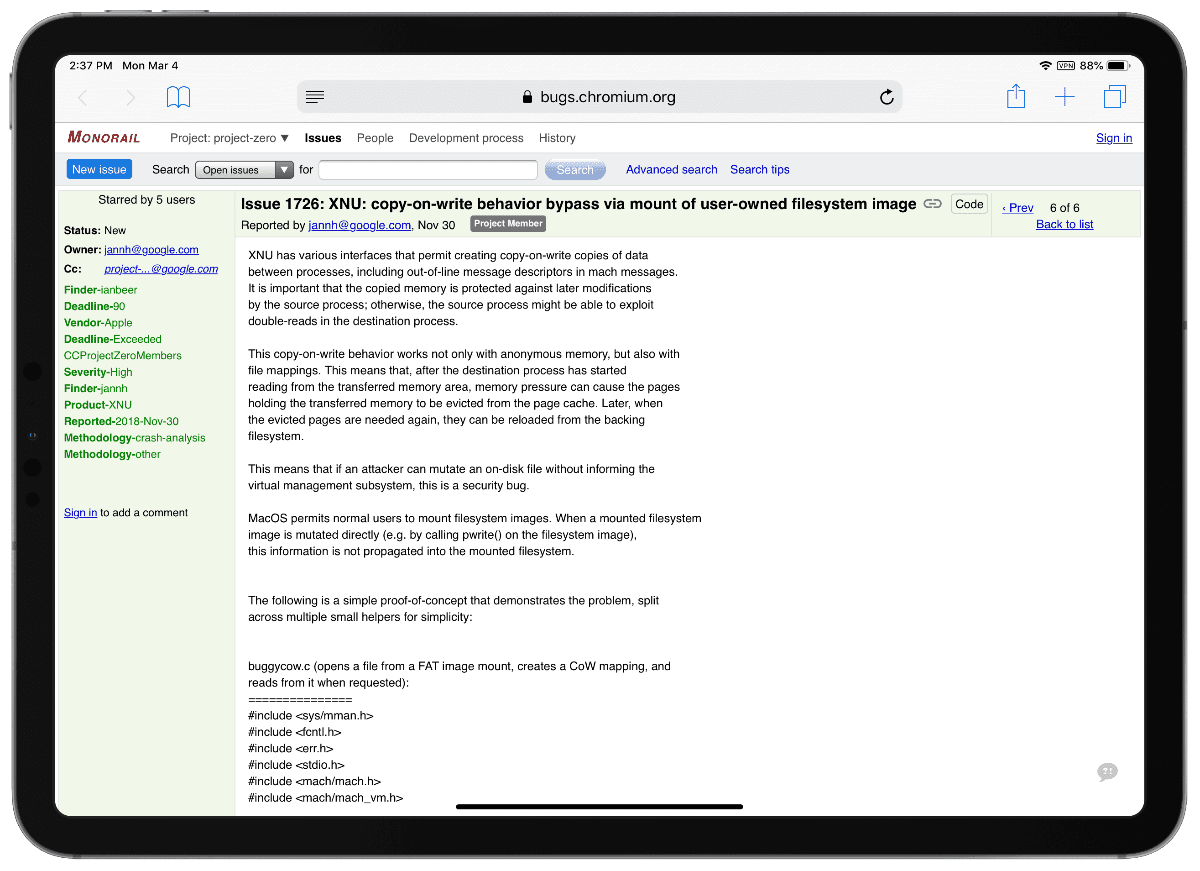
The flaw lets a hacker make changes to a file without informing the operating system. It messes with something called copy-on-write (COW), which lets processes write data between each other, but it’s supposed to be protected from other things modifying it. But the flaw lets it happen.
This copy-on-write behavior works not only with anonymous memory, but also with file mappings. This means that, after the destination process has started reading from the transferred memory area, memory pressure can cause the pages holding the transferred memory to be evicted from the page cache. Later, when the evicted pages are needed again, they can be reloaded from the backing filesystem.
Project Zero found the flaw back in November 2018. The team contacted Apple but no fix has been released yet.

What’s odd is that this seems like mostly correct behavior: if you page out a portion of an executable, then it is paged back in as needed from the file system, which seems reasonable.
The issue seems to be that the check for whether a signed executable has been modified happens at load time and isn’t repeated if the executable is modified (possibly maliciously) on disk during runtime, potentially allowing unsigned and malicious code or data to be loaded into a “signed” executable. Apple may be policing data loaded from the root file system, but apparently not for data loaded from mounted disk images, which may be writable by malicious code.
Please kids. Always use a VPN with a Mac – ALWAYS. Macs are just as easily exploited with malware as ANY PC – just look it up. The fact that Macs are only a TINY portion of the computing mkt is why we don’t get the VOLUME of attacks – but exploits are so easy thru your Browser especially Safari (use Firefox with all the 3rd pty protections) thru urls and links that contain scripts you’ll never even know about. Apple’s “alarms” for installing or opening files for the web are so easily by-passed they are virtually useless – a lot of times made so by the user’s negligence. VPN 👀
How is using a VPN going to change the malicious data that you are downloading from malware.com?
How is using a VPN going to fix security bugs in Safari? How will a VPN fix the “user’s negligence” as you put it and prevent users from installing a malicious web plug-in or visiting a phishing site?
Nothing wrong with VPNs, but they solve different problems (such as connecting semi-securely to a corporate intranet, or accessing Netflix when it is region-blocked.)
And does the hacker need physical access to the machine, a downloaded app?
How mature of them.
If I understood it correctly someone wouldn’t need physical access.
Then they should have kept their mouths shut until Apple fixed it.
You might find Bruce Schneier’s argument for full disclosure interesting. He argues that public scrutiny is how security improves:
https://www.schneier.com/blog/archives/2007/01/debating_full_d.html
90 days might be more than enough time to fix one line of code in a simple BASIC program, but perhaps not in something that is quite a bit more complicated. Apple hurries to fix the problem and in the process breaks something, that is my part of my argument. The other part is telling thief that the neighbor’s door key is under the welcome mat is irresponsible.
It seems to require you to download a disk image, run a program from it, and then modify the disk image maliciously while the first program is running.