GrowDiaries is a social media platform where marijuana growers can post about their plants and talk to other growers. Two of its servers leaked user data like usernames and passwords.
GrowDiaries Security Leak
Security researcher Bob Diachenko published a report on LinkedIn saying that GrowDiaries didn’t secure two of its Kibana apps used to manage Elasticsearch databases. As a result, one database with 1.4 million records exposed usernames, email addresses, and IP addresses, and the second database with 2 million records exposed passwords and user posts. Payment data was not exposed. The passwords were hashed using MD5, an algorithm known to be easily crackable.
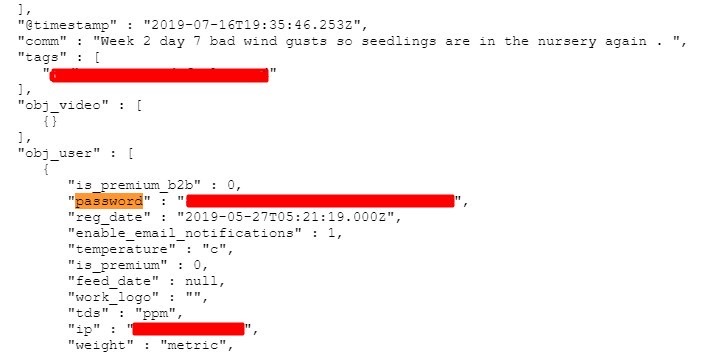
Mr. Diachenko discovered the databases on October 10, 2020. GrowDiaries acknowledged the breach and secured the data on October 15. The company hasn’t disclosed if the databases were accessed by unwanted third-parties, but Mr. Diachenko says this is likely as he isn’t the only one looking for insecure servers.