A team of researchers at TU Darmstadt discovered a flaw in AirDrop that could leak personal data. They notified Apple in May 2019 but the company hasn’t acknowledged the flaw or fixed it.
AirDrop Bugs
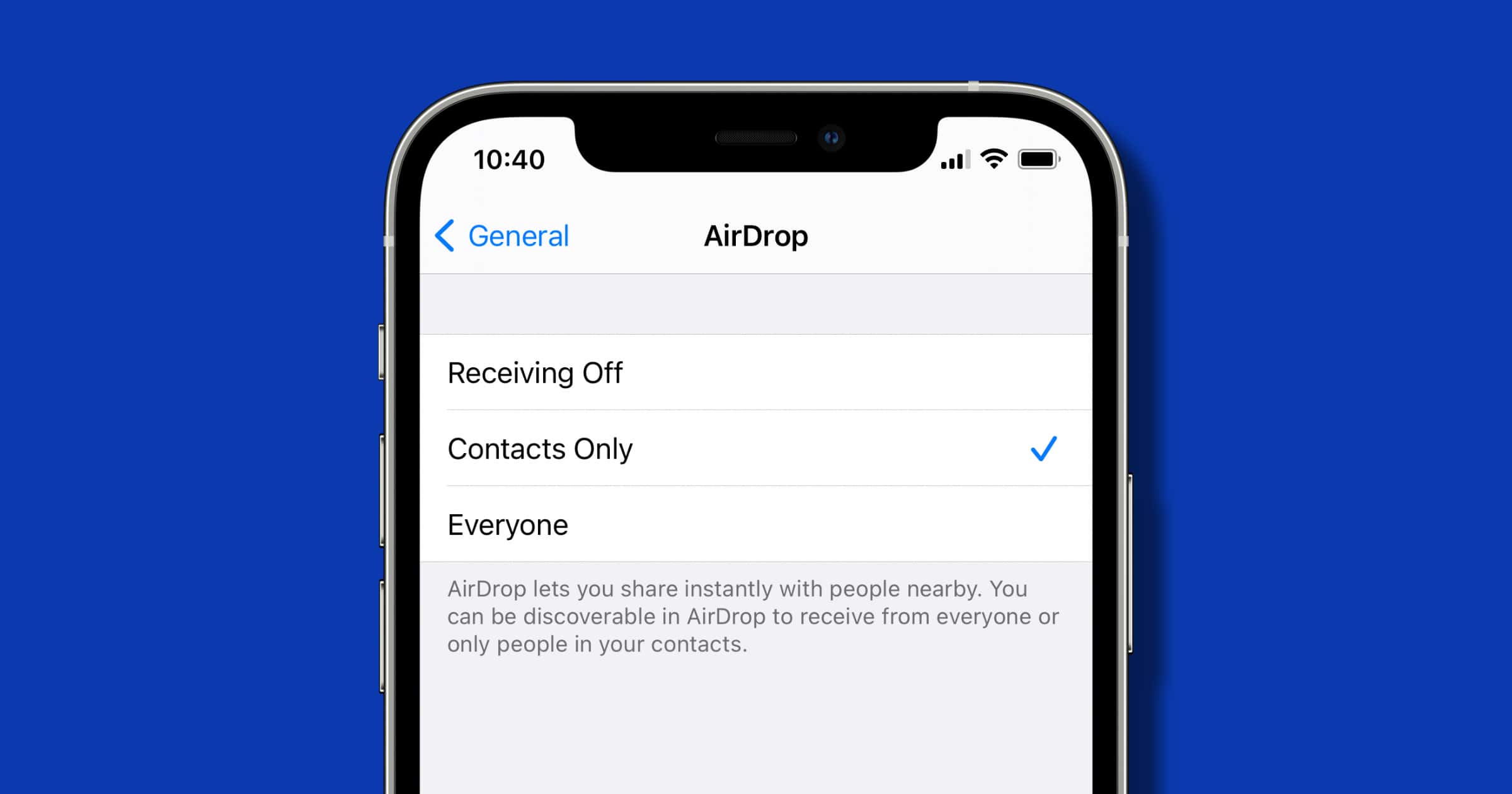
The team found that it’s possible to collect phone numbers and email addresses of AirDrop users, even if your Apple device has never associated with them via AirDrop. They didn’t go into details but all it requires is a Wi-Fi-capable device and close proximity to the victim.
But they also came up with a solution, dubbed “PrivateDrop.” It replaces the original AirDrop and is based on “optimized cryptographic private set intersection protocols that can securely perform the contact discovery process between two users without exchanging vulnerable hash values.”
Interestingly, 2019 was the year a separate flaw in AirDrop was found, this one from Kishan Bagari. Known as “AirDOS” it let an attacker spam surrounding iOS devices with AirDrop pop up notifications. In that case, Apple did acknowledge the flaw and patched it with iOS 13.3.