SimJacker is a newly-discovered vulnerability in SIM cards that lets an attacker hack your smartphone just by sending an SMS message (via Hacker News).
SimJacker
The vulnerability resides within a piece of software on SIM cards called the S@T Browser. Short for SIMalliance Toolbox Browser, it was designed to let carriers provide basic services to their customers. Even eSIM technology is affected. A “specific private company” has already been working with governments to exploit it.
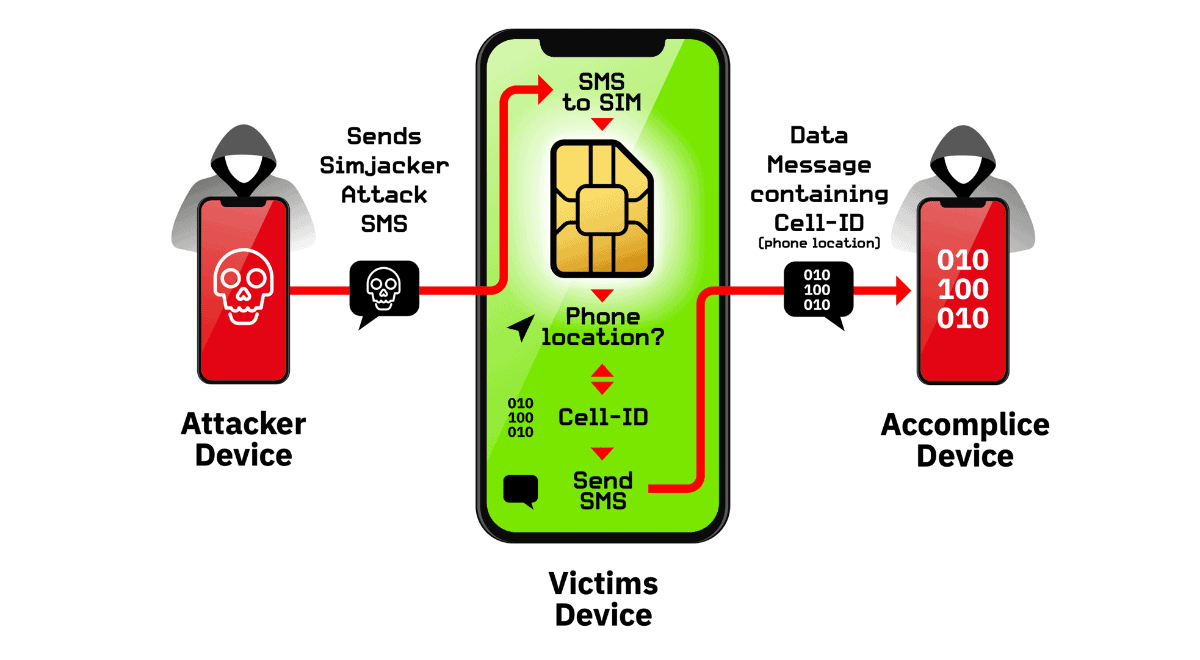
Since S@T Browser contains a series of STK instructions—such as send short message, setup call, launch browser, provide local data, run at command, and send data—that can be triggered just by sending an SMS to a device, the software offers an execution environment to run malicious commands on mobile phones as well.
The researchers say that all manufacturers and mobile phone models are vulnerable to SimJacker. Mobile operators can put a stop to it by setting up processes to analyze and block suspicious messages that contain S@T Browser commands.

Another day, another major hack, data breach or vulnerability. I am really starting to think about how to do computing without an Internet/wireless network connection.
Hopefully they will.