Dreamlight Valley resident and TMO Managing Editor Jeff Butts joins Ken today to discuss Apple’s Advanced Data Protection for iCloud. What is it, who needs it, and how does one activate it? Plus – Will Smith is promoting Apple TV+. Too soon?
FBI
FBI Launches Virtual Asset Exploitation Team
The U.S. Federal Bureau of Investigation is launching the Virtual Asset Exploitation Team (VAXU) to investigate crypto-crime.
Security Friday: Actually Some Good News – TMO Daily Observations 2022-02-18
Andrew Orr and Kelly Guimont discuss the Security Friday news of the week including deepfake scams and nefarious AirTag schemes.
FBI Warns of Money Transfer Scams Over Video Calls
The FBI is warning consumers to be aware of scammers impersonating high-level company executives to trick employees into transferring money.
FBI: BlackByte Ransomware Attacks Critical Infrastructure
The FBI and Secret Service have seen signs of BlackByte ransomware attacking at least three critical infrastructure sectors in the U.S.
FBI Flash Report Warns of Attacks With LockBit 2.0 Ransomware
The FBI has issued a flash report this week that details indicators of compromise (IOC) linked to LockBit 2.0 ransomware.
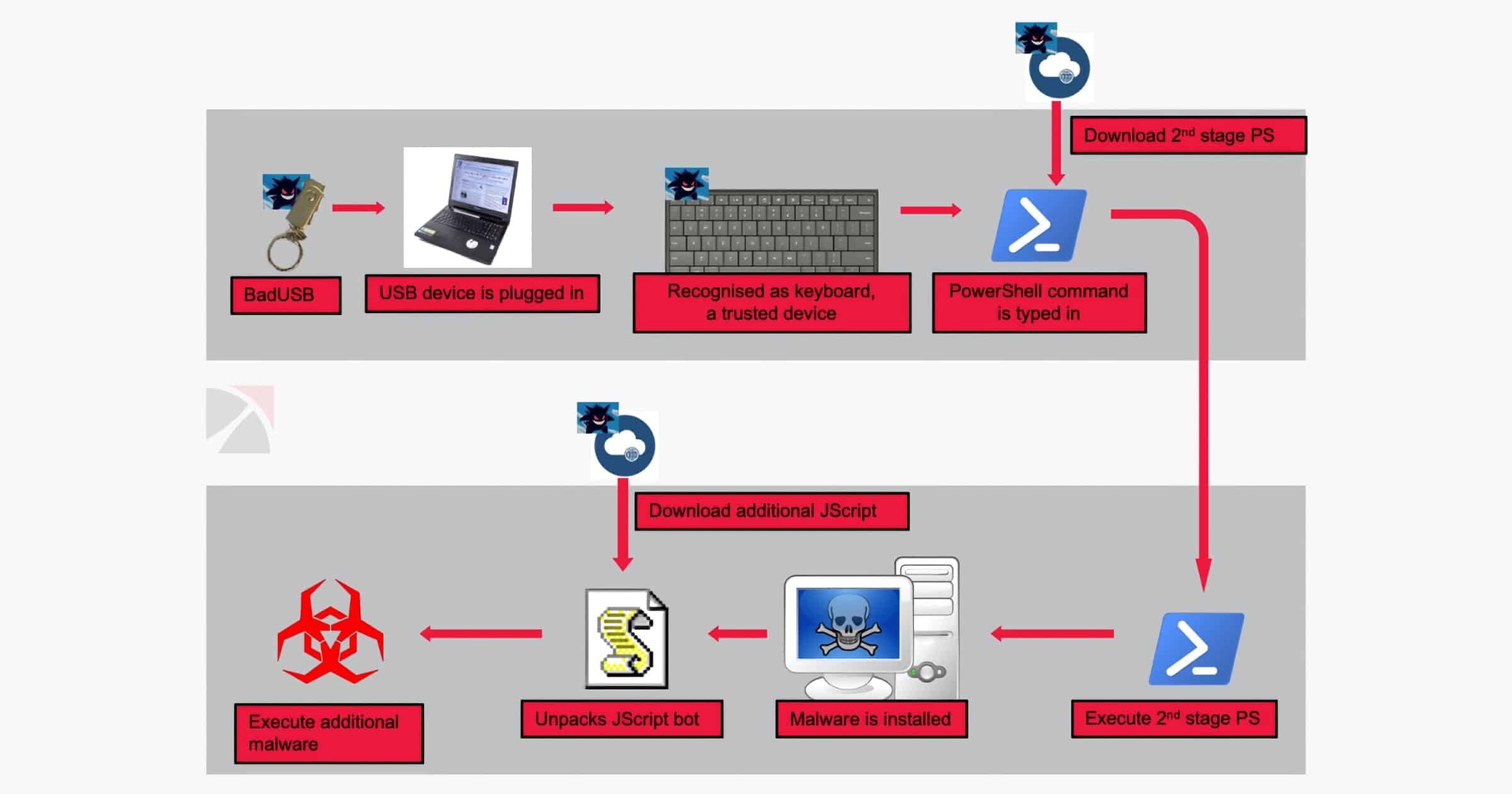
People are Mailing USB Drives With 'BadUSB' Malware to Companies
The FBI is warning that an Eastern European cybercriminal group is mailing USB drives filled with BadUSB malware to various companies.
FBI Says Data Was Not Compromised After Hackers Took Over Email Server
Hackers took over an FBI server over the weekend, sending thousands of fake cyberattack warnings. The agency says no personal information or data was affected.
The agency said it has fixed the software vulnerability that allowed the attack.
The fake emails originated from an FBI-operated server, which was dedicated to pushing notifications to the Law Enforcement Enterprise Portal (LEEP), which the FBI uses to communicate with state and local agencies. The compromised server was not part of the FBI’s corporate email service, the FBI added.
Security Friday: Bug Bounties, Updates, and Tools for "Good Guys" – TMO Daily Observations 2021-10-29
Andrew Orr joins host Kelly Guimont to discuss Security Friday news and updates including who can get into your phone now, and a massive bug bounty.
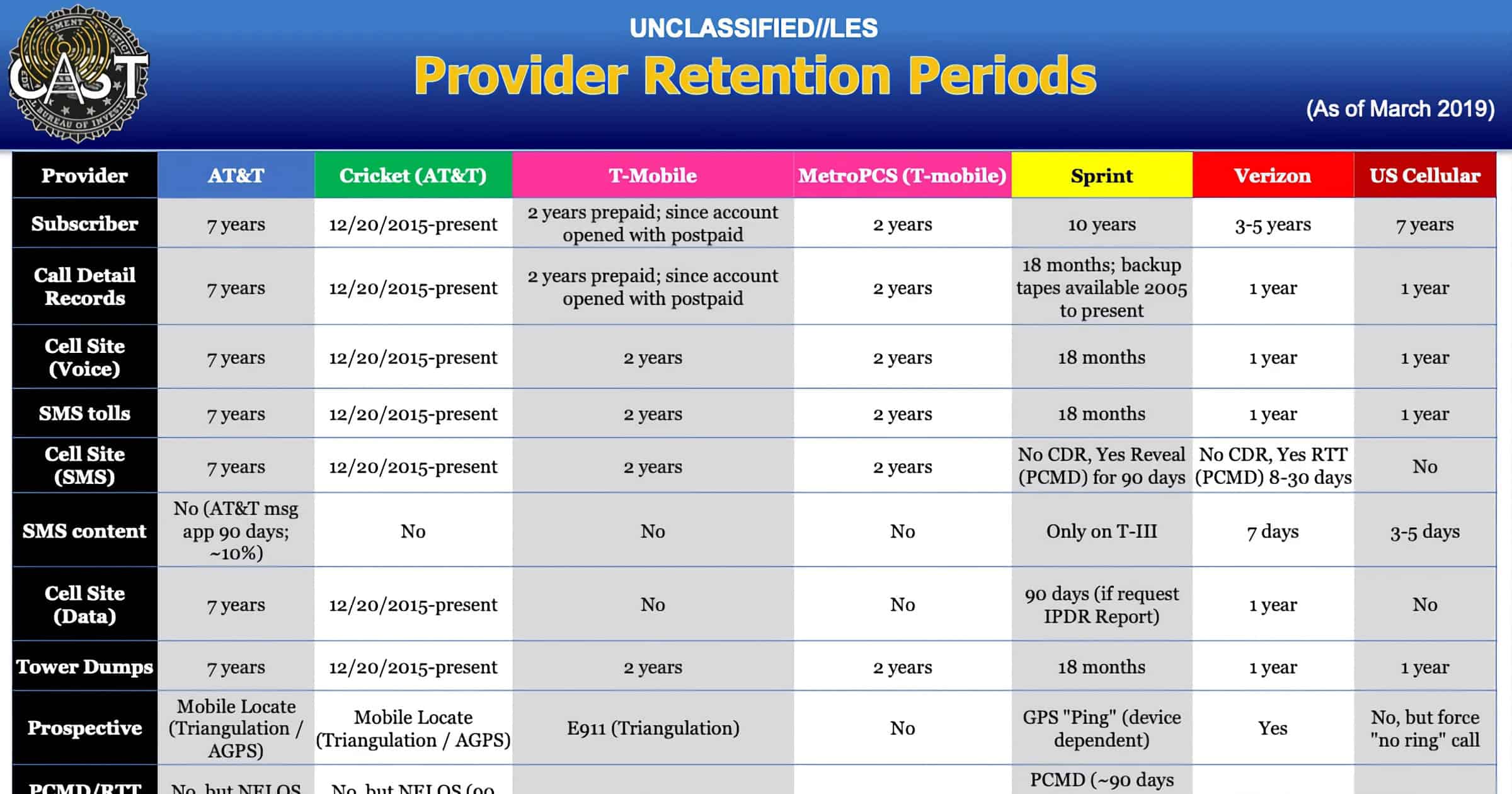
FBI Document Reveals Guide to Get Location Data From Carriers
An internal document for the FBI reveals how the agency obtains phone location data from carriers like AT&T, Verizon, and others.
'REvil' Ransomware Group Taken Down Through Multi-Country Effort
The FBI, working with Cyber Command, the Secret Service, and other countries, took down REvil.
According to three people familiar with the matter, law enforcement and intelligence cyber specialists were able to hack REvil’s computer network infrastructure, obtaining control of at least some of their servers. After websites that the hacker group used to conduct business went offline in July, the main spokesman for the group, who calls himself “Unknown,” vanished from the internet.
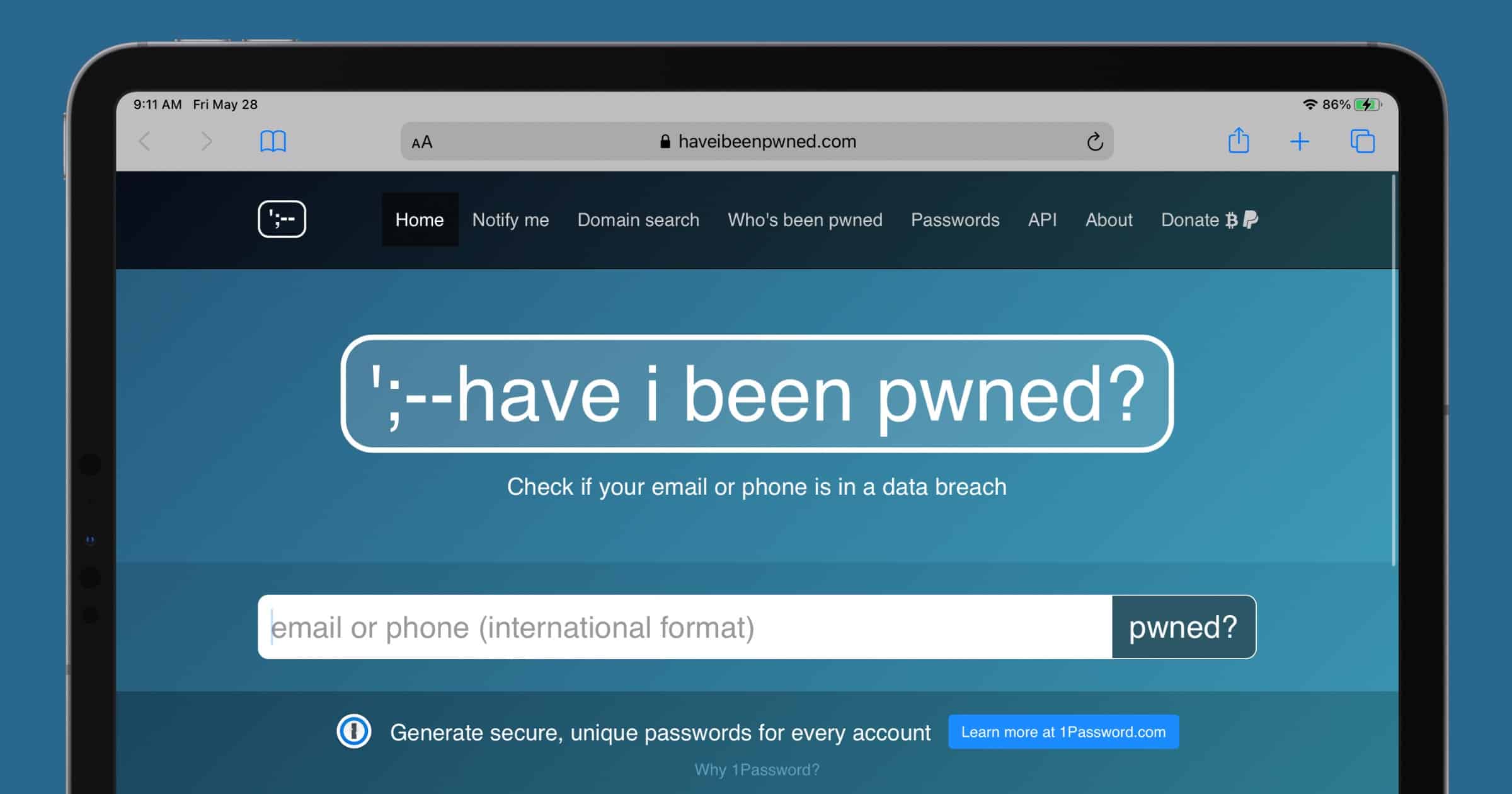
‘Have I Been Pwned’ Open Sourced, Partners With FBI
The popular service Have I Been Pwned has made its code open source, and it’s also partnering with the FBI. The agency will send compromised passwords discovered during investigations.
Why is the FBI getting involved? Because Bryan A. Vorndran, the FBI’s Assistant Director, Cyber Division, said, “We are excited to be partnering with HIBP on this important project to protect victims of online credential theft. It is another example of how important public/private partnerships are in the fight against cybercrime.”
Security Firm Behind iPhone Unlocking Finally Discovered
The security firm that unlocked the iPhone of the San Bernardino shooter has been unveiled, and it’s an Australian company called Azimuth.
Azimuth is a poster child for “white hat” hacking, experts say, which is good-guy cybersecurity research that aims to disclose flaws and disavows authoritarian governments. Two Azimuth hackers teamed up to break into the San Bernardino iPhone, according to the people familiar with the matter, who like others quoted in this article, spoke on the condition of anonymity to discuss sensitive matters.
An interesting story, especially with the connection to Corellium.
How the U.S. Used the Patriot Act to Track Web Browsing
Government entities have been using Section 215 of the Patriot Act as justification to collect logs of web browsing activity.
In fact, “one of those 61 orders resulted in the production of information that could be characterized as information regarding browsing,” Mr. Ratcliffe wrote in the second letter. Specifically, one order had approved collection of logs revealing which computers “in a specified foreign country” had visited “a single, identified U. S. web page.”
FBI Warns of Ransomware Threat to US Healthcare System
The FBI, CISA, and HHS are issuing a joint alert to warn of the threat of ransomware attacks currently affecting U.S. healthcare systems.
Apple Gave FBI Access to Rioter’s iCloud Account
According to court documents, Apple gave the FBI access to a rioter’s iCloud account who was accused of setting police cars on fire in Seattle this summer.
As FBI officers were investigating a Seattle man suspected of setting police cars on fire, they turned to Apple for help […] Apple disclosed the name, email, phone number, and residential address associated with Jackson’s account, then subsequently granted the FBI access to the contents of Jackson’s account in response to a court-ordered search warrant.
Apple was served a lawful subpoena in regards to a lawful investigation, as it does frequently. But the main point is that it contrasts with claims from President Trump and A.G. Barr that Apple hinders investigations because they can’t unlock iPhones. Apple can’t do that, but if a person backs content up to iCloud, then it can be accessed.
FBI Worries That Doorbell Cameras Could Give Early Warning of Police Searches
A leaked FBI bulletin reveals that doorbell cameras like Ring are being used to alert people when police show up for searches. It’s a funny turn of events since law enforcement agencies actively encourage people to install these cameras.
Subjects likely use IoT devices to hinder LE [law enforcement] investigations and possibly monitor LE activity. If used during the execution of a search, potential subjects could learn of LE’s presence nearby, and LE personnel could have their images captured, thereby presenting a risk to their present and future safety.
Senate Vote Lets FBI View Your Browsing History Without Warrant
As part of a reauthorization of the Patriot Act, the Senate voted to let the FBI access Americans’ web browsing history without a warrant. I could say a lot of bad things about this, but this is the part that disappoints me the most:
Sens. Ron Wyden (D-OR) and Steve Daines (R-MT) attempted to remove the expanded powers from the bill with a bipartisan amendment.
But in a shock upset, the privacy-preserving amendment fell short by a single vote after several senators who would have voted “Yes” failed to show up to the session, including Bernie Sanders. 9 Democratic senators also voted “No,” causing the amendment to fall short of the 60-vote threshold it needed to pass.
Just one vote.
The FBI is Collecting Your Data Through its ‘FitTest’ App
The FBI has been promoting its fitness app called FitTest to help people exercise at home. It’s also collecting your data.
…an FBI spokesperson reiterated the app’s privacy statement, adding that “the app does not gather or save any personal information other than what you select for your profile.”
But the app’s privacy statement makes room for some tracking: When FitTest accesses pages from the official FBI website, it says, “fbi.gov’s privacy policy applies.” The fbi.gov privacy policy states that “individuals using this computer system are subject to having all of their activities monitored and recorded.”
I can’t wait for the FBIPhone and FBIMessage apps.
FBI Investigates Over 1,000 Cases of Chinese IP Theft
At the China Initiative Conference, government officials from the FBI and DoJ spent four hours talking about theft of U.S. intellectual property by China.
“The threat from China is real, it’s persistent, it’s well-orchestrated, it’s well-resourced, and it’s not going away anytime soon,” John Demers, Assistant Attorney General for National Security, opened the conference.
“This one to me really stands out as the greatest long-term threat to our nation’s information and intellectual property, and to our economic vitality,” said FBI Director Christopher Wray.
Apple and the FBI – TMO Daily Observations 2020-01-21
Bryan Chaffin and Andrew Orr join host Kelly Guimont to discuss Apple’s decision not to encrypt backups, and what data Apple can share.
Apple Cancels iCloud Encryption Plan Due to FBI
Apple had plans to introduce end-to-end encryption for iCloud backups, but canceled it two years ago after the FBI complained.
ACLU, EFF Join Apple in Renewed Encryption Battle
The American Civil Liberties Union and the Electronic Frontier Foundation are joining Apple in its encryption battle with the government.
Attorney General Barr Asks Apple to Break Encryption
Attorney General William Barr has asked Apple to unlock the iPhone used by the shooter in Pensacola, Florida.