Your Mac has a history of everything you’ve ever downloaded, but it’s possible to clear it out. Viewing your Mac download history requires using the Terminal, so it’s unlikely most users would know how to do this. Here’s how to view and clear it.
Viewing Mac Download History
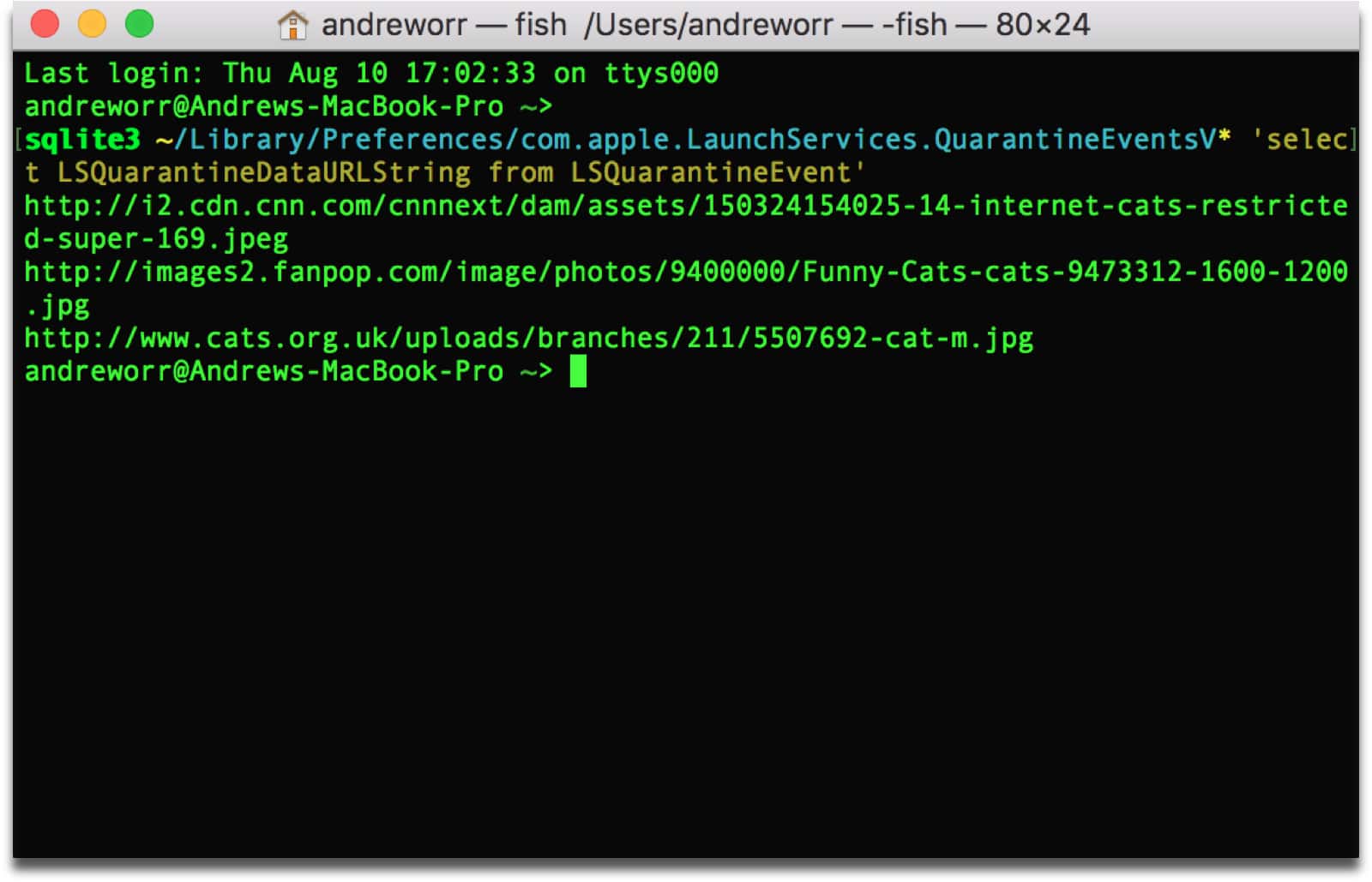
Here is a command that you can simply copy and paste into your Terminal to view your Mac download history:
sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV* 'select LSQuarantineDataURLString from LSQuarantineEvent'
This isn’t just Safari downloads. Any app that lets you download files will show up here. This can include torrents, cat photos, porn—anything. This happens because your Mac has used a Quarantine Manager since OS X Snow Leopard. It means that your Mac checks each download for safety issues, so you don’t unknowingly download a virus (although it could still happen.)
Clear Mac Download History
Here’s how to delete the history. Again, this is command you can copy and paste into your Terminal:
sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV* 'delete from LSQuarantineEvent'
However, your Mac will continue to keep a history, so you’ll need to run these commands every now and then if you want to clear it out.
Automated Cleaning
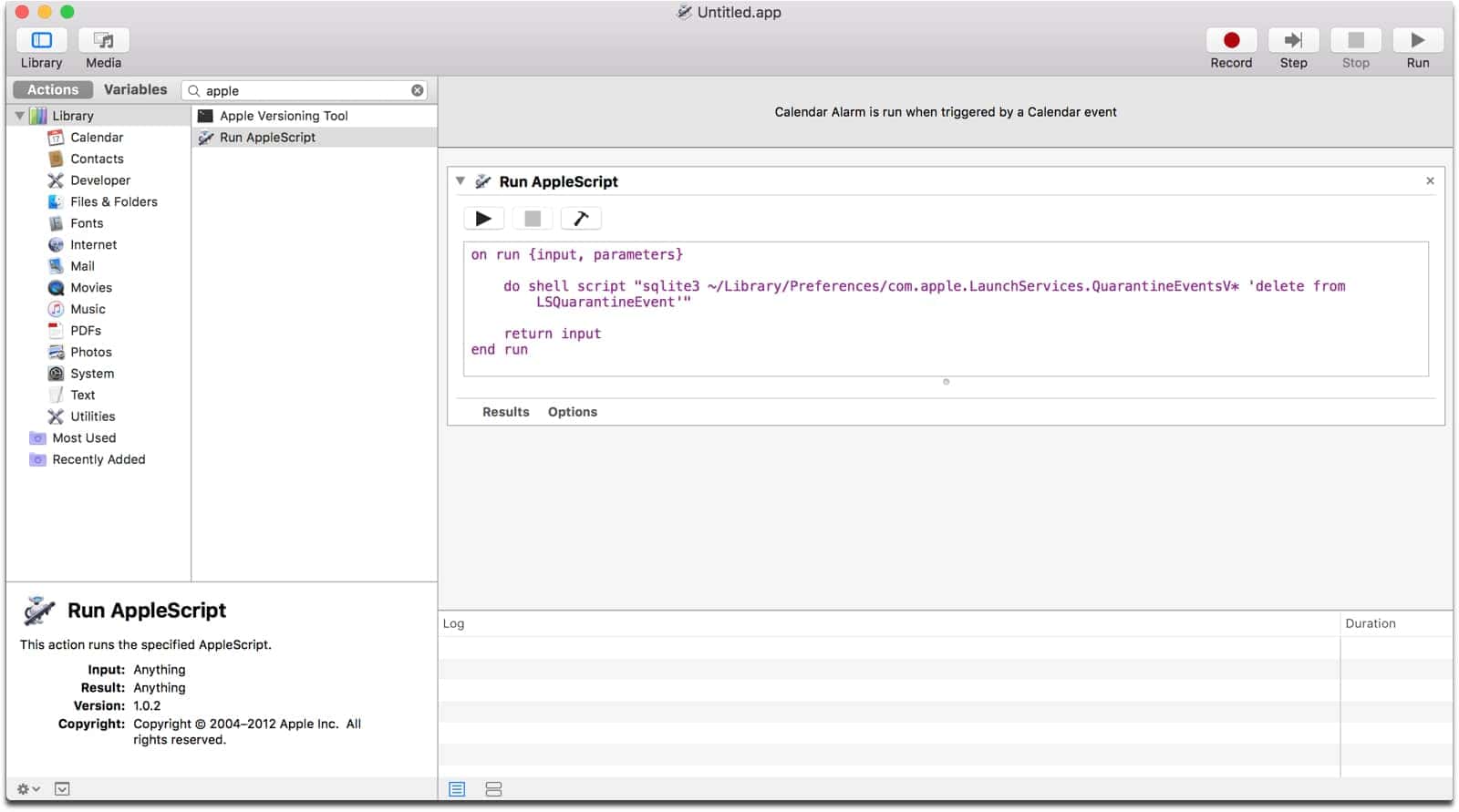
As power users, we all like to automate things, so in order to have your Mac automatically clear its history, we can create a Calendar Alarm using Automator. In the sidebar, you can search for “Run AppleScript” and drag it into the work area.
do shell script "sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV* 'delete from LSQuarantineEvent'"
Copy and paste the above command into the window. Basically, you’ll just be replacing the default text that says (* Your script goes here *).
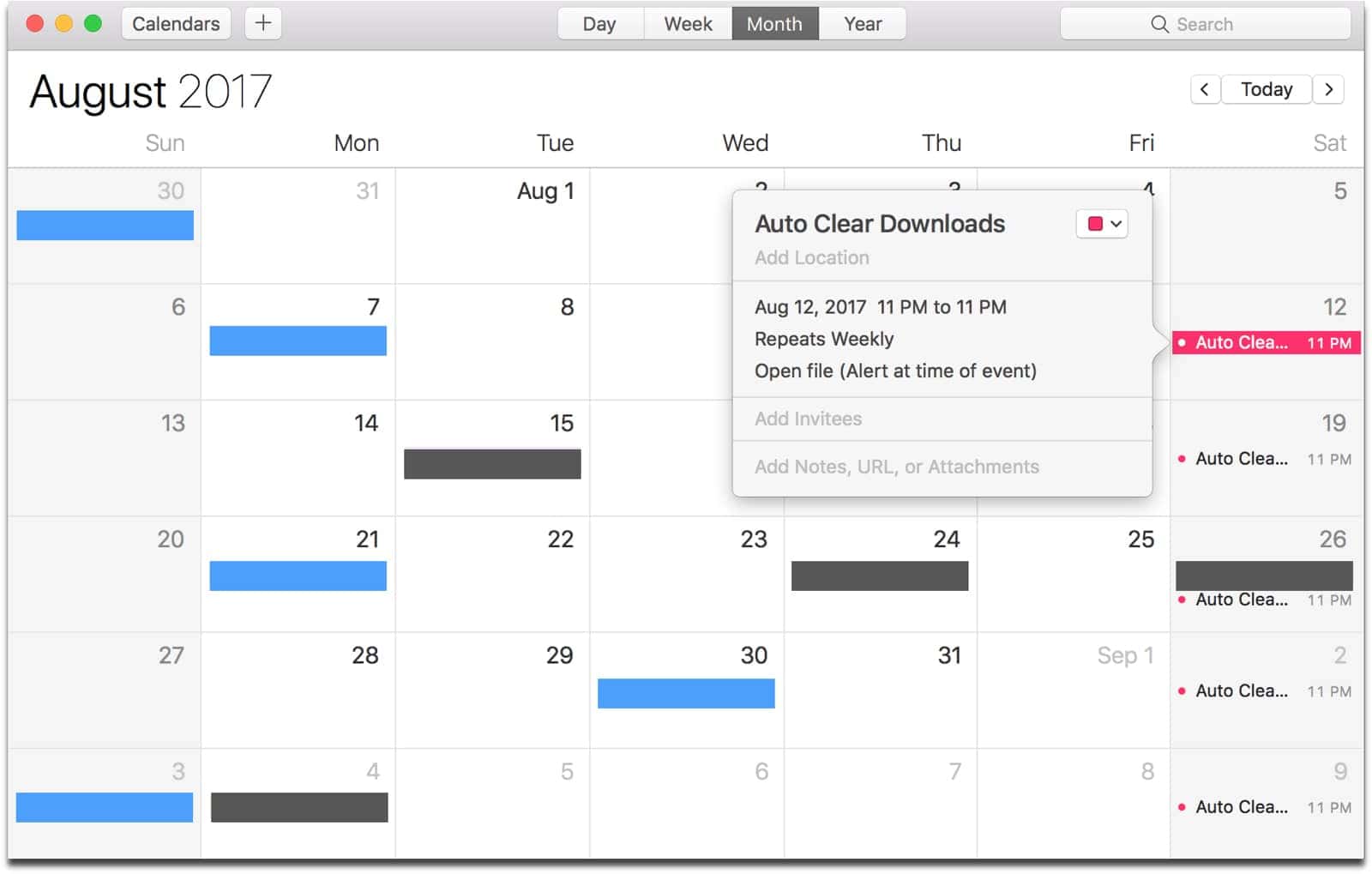
When you save the file, it will automatically create a separate Automator calendar in the Calendar app. This will of course be in the On My Mac section, and not an iCloud calendar. Saving the file will have it run immediately, and only once. But you can edit the event in Calendar to have it run on a specific schedule. I have mine run every Saturday at 11PM.
Unfortunately the listed commands don’t quite have the desired effect.
I was suspicious that the file size hadn’t changed, so opened it up in a text editor and the raw data was still present despite a zero result from count(*).
The additional command that is required is ‘vacuum’ to tell sqlite to rebuild the database file:
sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV2 ‘vacuum LSQuarantineEvent’
Fantastic find! I wouldn’t have thought to check this. Thanks for sharing the info and solution!
vacuumdoesn’t seem to benefit me, but after reading this post/comments again years later I realize there are 3 named databases, of which only 2 apply. From terminal:ls -l ~/Library/Preferences/com.apple.LaunchServices.QuarantineEvents*and querying against all three, only the non-V and V2 have table
LSQuarantineEventSo by following the code provided you never hit the non-V table, which also appears to contain download history.
I updated my script to delete records from both com.apple.LaunchServices.QuarantineEventsV2 and com.apple.LaunchServices.QuarantineEvents
Thanks for the info, but It appears that this may not work with High Sierra (public beta). I’ve tried…
sudo sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV* ‘select LSQuarantineDataURLString from LSQuarantineEvent’, both with the V* and the V2 and, in both cases, nothing is returned. I haven’t been using any other means to clear my download history, so I’m sure that the data is there, somewhere.
You have an error. There is a file com.apple.LaunchServices.QuarantineEventsV* (with the asterisk) that is empty. People need to replace the splat (asterisk) with a 2 so that it looks for the file com.apple.LaunchServices.QuarantineEventsV2.
It is not a good style to rely on wildcards for system-related services. You should ALWAYS use exact file names. If the name has an asterisk I highly recommend that you should quote or escape it to make sure there is no ambiguity. After a little Google-fu, which I suggest when you write something like this, it appears that if there ever was a problem with the Quarantine services that it will create the V2 file.
Second, if you want to see the list of URLs, you need to change the select statement to:
select LSQuarantineDataURLString from LSQuarantineEvent where LSQuarantineDataURLString != ”;
(those are two single quotes with nothing between them) This will get rid of blanks in the file.
Third, if you are going to do this, I would recommend deleting the file in its entirety. Even though you delete the records in the database, space is not released back to the filesystem. It is still the same file. You can still crawl through the file using other tools and look for the various URLs. Go find an sqlite recovery tool and see what I mean. By deleting the file you release the blocks back to the filesystem where they could be reused. (I also do infosec for a living and have used forensic tools to crawl through sqlite databases looking for incriminating evidence)
If you are using Yosemite, you cannot do a secure delete from the command line because Apple removed the command. If you are using El Capitan, you can use the “srm” command to securely remove the file. There are utilities you can buy to do this or you can use “diskutil” and ask it to do a “secureErase” on “freespace” only and hope that doesn’t destroy things!
The secure delete has other issues, such as its writing over files with zeros and/or a pattern. You cannot do this on an SSD or even a Fusion drive. Aside from burning out the memory, on a Fusion drive, you do not know if data was cached at one point on the SSD portion of the drive. Therefore, a secure delete is not recommended. However, removing the file is a far better option than just deleting database records!
Hi Scott, thanks for the information. I’ll do more testing with those modified commands, as well as the SQLite database and its deletion/impact.
I would not recommend deleting the database files as there is more than just the download data table there.
Andrew, thanks for the tip, but perhaps you could try actually following your own instructions ?
Maybe my brain isn’t plugged in this morning ?
But the steps for creating a a Calendars event that runs the clear history script is missing steps / details ?
regards
furbies
launch automator, create a calendar event, then on the left pane choose from library / utilities / run AppleScript – drag it to the calendar event pane you created on the right and then you’ll see the code box for his instructions above.
Fascinating. I didn’t find as much there as I would have expected. Does it maybe get cleared out after an upgrade (even a point upgrade)?
There is a timestamp column in the table that contains numbers that look like 452529740.633129. They don’t appear to be large enough to be Unix epoch’s, plus their is a decimal component which epochs usually don’t have. I can’t get strftime to return anything but NULL, no matter what options I try. Anyone know what that is and how to coerce a readable date/time out of it?
Grrrr; “…plus there is a decimal component…”.
It’s possible that upgrades might clear it out; I don’t know for certain though. Also, if I understood your comment correctly, you could try this command in order to see timestamps of each download entry:
sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV* ‘select LSQuarantineTimeStamp, LSQuarantineDataURLString from LSQuarantineEvent’ | php -r ‘date_default_timezone_set(“America/Montreal”); foreach (explode(“\n”, file_get_contents(“php://stdin”)) as $l) { preg_match(“/([0-9\.]+)\|(.*)\$/”, $l, $re); echo date(“Y-m-d H:i:s”,strtotime(“2000-01-01 19:00″)+$re[1]).”\t$re[2]\n”; }’
Answering my own question: after a bit more searching, it appears that they are # of days, but they start at 2001-01-01 (initial date of OSX) instead of Unix’s epoch. Adding the # of days in-between allows datetime() to return a valid value. (I still don’t know what the decimal is all about, but it returns a date close enough to reality for my current purposes.)
I’m getting the error in the terminal.
Try this command to see if it will work:
sqlite3 ~/Library/Preferences/com.apple.LaunchServices.QuarantineEventsV* ‘select LSQuarantineDataURLString from LSQuarantineEvent’ > ~/Desktop/QuarantineEventList.txt
This will create a text file on your desktop with the download history.
There we go, thank you. 🙂 Very cool tip. I knew about the file quarantine, I didn’t know it was so accessible. Really enjoying the more power user-oriented articles.
Excellent, Andrew, but I keep getting a ‘too many options’ error. Any idea why that might be the case?
Hi Jamie, at which point are you seeing that error? In the terminal or in Automator?