A China-based hacking group known as APT27 has been targeting German companies in areas such as technology and pharmaceuticals. Germany‘s domestic intelligence service Bundesamt für Verfassungsschutz (BfV) put out the warning.
APT27 Hacking Group
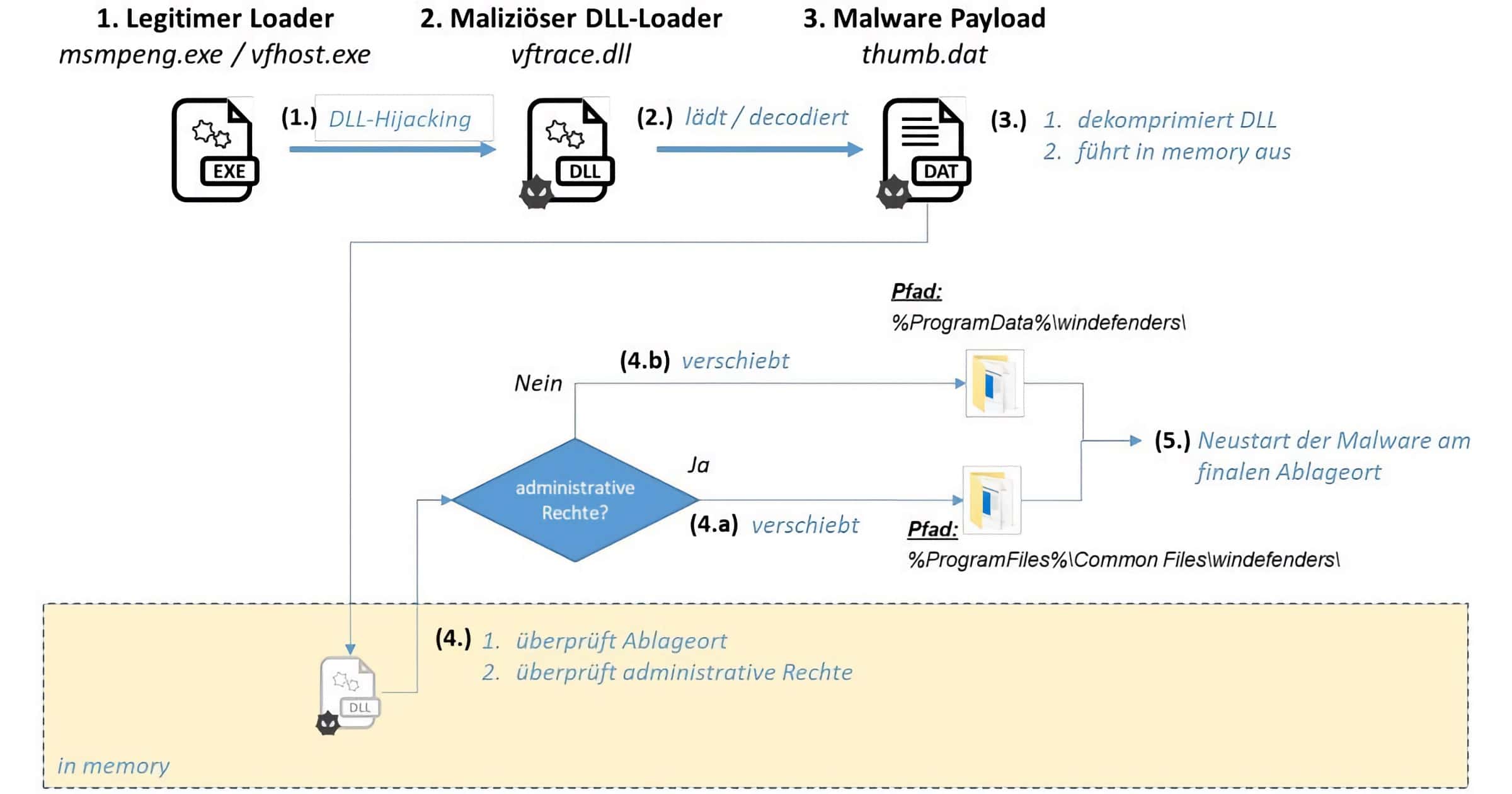
APT27 has been using a remote access trojan (RAT) called HyperBro. The trojan consists of three or more components: A genuine loader typically with a signed certification, a malicious DLL loader loaded from the former component via DLL hijacking, and an encrypted and compressed blob that decrypts to a PE-based payload with a hardcoded command and control (C2) server.
BfV says that APT27 has been targeting vulnerabilities within Microsoft Exchange and Zoho AdSelf Service Plus1 software. The group is believed to have been attacking these companies since March 2021. Possible goals of the attacks include theft of trade secrets and/or intellectual property, or using the networks of these companies as a stepping stone for supply chain attacks.
APT27, also known under names such as Emissary Panda, TG-3390, Iron Tiger, LuckyMouse, and BRONZE UNION, has been active since 2010. This group typically carries out cyber espionage and information theft, as BfV reports. The agency has published [PDF] indicators of compromise (IOCs) and YARA rules so German companies can check for HyperBro infections.
According to Bleeping Computer, the hacking group “first used an ADSelfService zero-day exploit until mid-September, then switched to an n-day AdSelfService exploit, and started exploiting a ServiceDesk bug beginning with October 25.” Those attacks successfully compromised at least nine companies in various industries such as energy, healthcare, and education.
Andrew:
That German companies specifically, of all EU companies, are being targeted at this time suggests that, apart from IP theft (always a plus), a primary objective is likely supply chain interruption.
China appear to be coordinating with Russia in stepping up pressure on the West, specifically the USA, and testing their resolve as a global superpower to protect vulnerable interests and allies, like the Ukraine (Russia) and Taiwan (China), with the likes of North Korea and Iran nipping at the edges (eg the former launching missiles in the direction of allies, the latter with proxy attacks on UAE via Yemen).
The weak link in NATO resolve regarding pushing back against Russia possibly invading Ukraine is Germany, and its reliance on the Russian gas pipeline. If other elements of their logistics and supply chain can be compromised, this would be a classic pincer move that could remove Germany from the chessboard altogether, and strengthening Putin’s hand.
One has to admire the strategy, even if the objectives are repugnant.