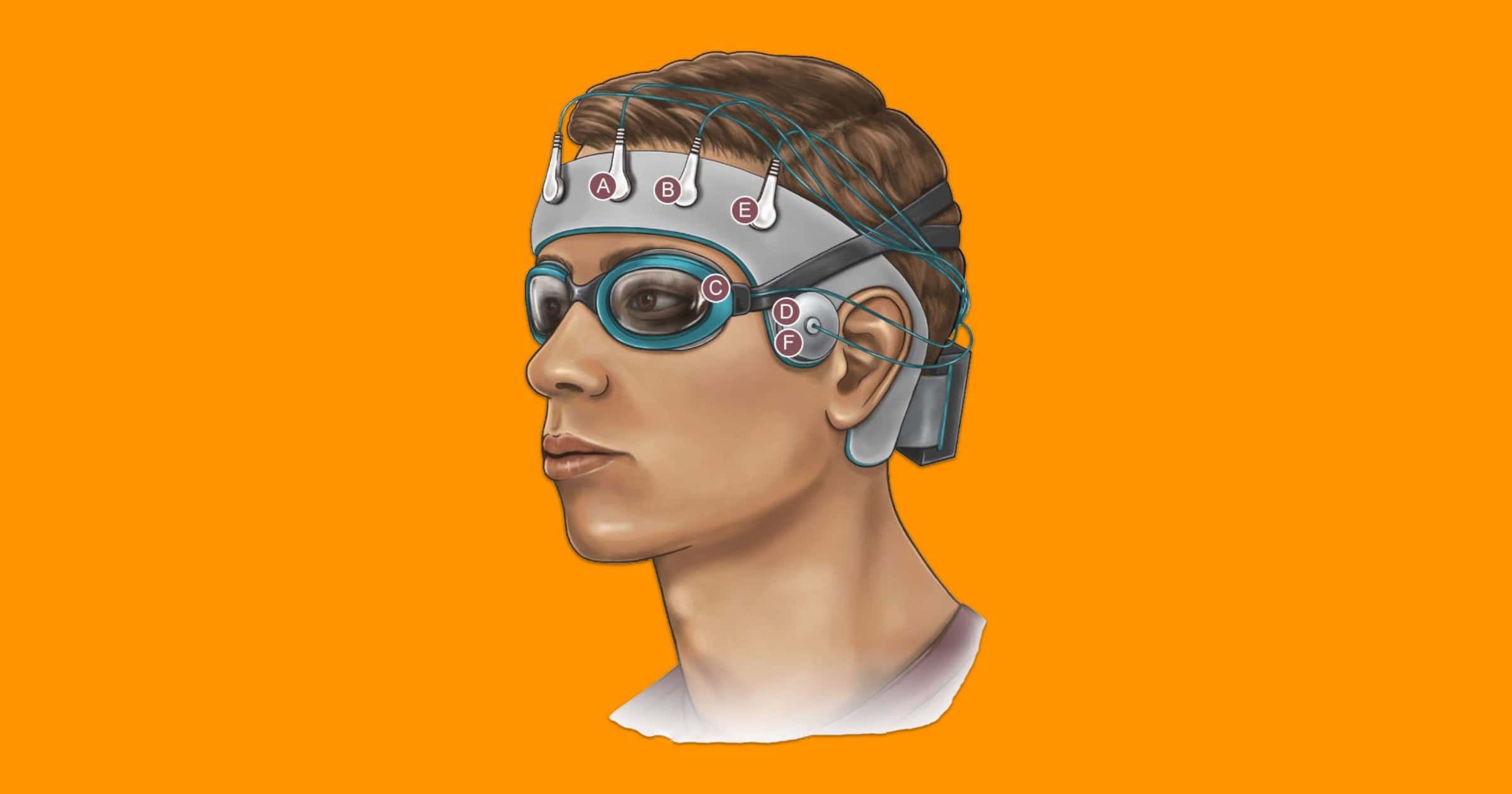
The U.S. Army is funding a special skullcap that aims to analyze how the brain disposes of waste during sleep. Eventually, the goal is for the device to treat sleep disorders for soldiers in real time.
The $2.8 million award issued through the Medical Technology Enterprise Consortium is for the first year of what the research team anticipates will be a multiyear grant from the U.S. Army. The primary goal is to noninvasively measure and modulate the flow of cerebrospinal fluid as it circulates through the brain and clears waste.
I can’t resist linking to Galactic Cowboys.