British police recently arrested seven people, aged 16 to 21, as part of its investigation into the group of Okta hackers known as Lapsus$.
ransomware
Here's What We Know About PYSA Ransomware
PYSA ransomware is a piece of malware from an unknown APT group. It attacks what the FBI calls “soft targets.”
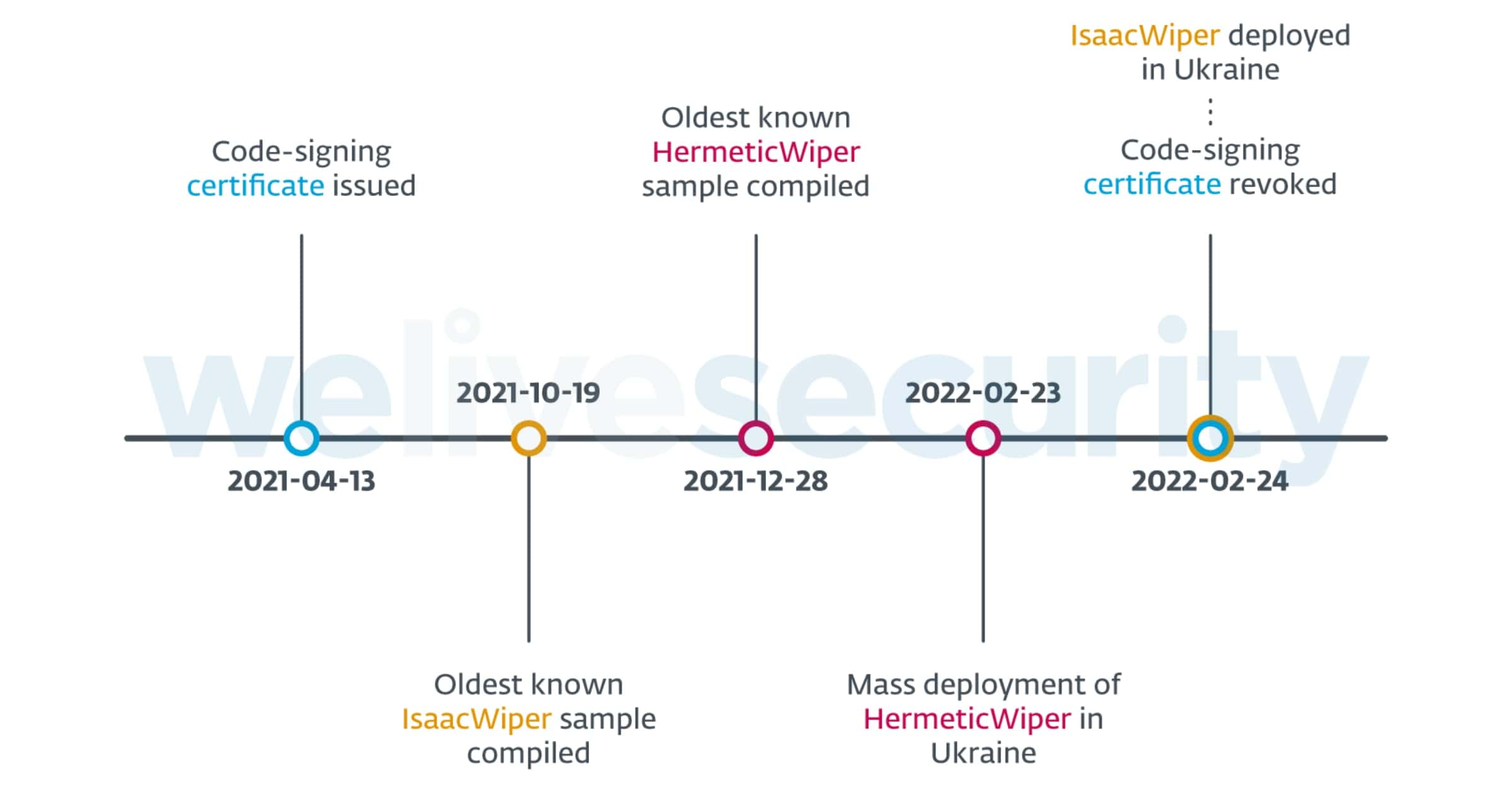
Security Firm Examines Recent Cyberattacks Against Ukraine
Entities in Ukraine have been targeted by hackers that wipe hard drives of all data. An investigation from PCMag reveals what has happened.
FBI: BlackByte Ransomware Attacks Critical Infrastructure
The FBI and Secret Service have seen signs of BlackByte ransomware attacking at least three critical infrastructure sectors in the U.S.
FBI Flash Report Warns of Attacks With LockBit 2.0 Ransomware
The FBI has issued a flash report this week that details indicators of compromise (IOC) linked to LockBit 2.0 ransomware.
Information Superhighway...to Hell – TMO Daily Observations 2022-01-14
Andrew Orr and Kelly Guimont discuss the latest security news including a happy headline, a practical tip, and an uplifting sendoff to the weekend.
Russian Authorities Arrest Members of REvil Ransomware Group
The Russian Federal Security Service (FSB) announced on Friday that it has arrested 14 members of the REvil ransomware group.
Ransomware Attack on Finalsite Shuts Down 5,000 School Websites
Finalsite is a company that helps schools with websites. In a statement, it says it was hit by a ransomware attack on Tuesday, January 4.
Security Friday: No News is Good News – TMO Daily Observations 2021-12-10
Andrew Orr and Kelly Guimont discuss Security Friday topics. They say no news is good news, and this week is FULL of news.
Government Traces Ransomware Payments to Business Address in Moscow
The New York Times writes how the U.S. government has traced ransomware payments to an address in Federation Tower East in Moscow, Russia.
That this high-rise in Moscow’s financial district has emerged as an apparent hub of such money laundering has convinced many security experts that the Russian authorities tolerate ransomware operators. The targets are almost exclusively outside Russia, they point out, and in at least one case documented in a U.S. sanctions announcement, the suspect was assisting a Russian espionage agency.
Cuba Ransomware Gang Made $43.9 Million in Ransom Payments
The FBI also said it traced attacks with Cuba ransomware to systems infected with Hancitor. This is a malware operation to access Windows machines.
It is also worth mentioning that Cuba is also one of the ransomware groups that gather and steal sensitive files from compromised companies before encrypting their files. If companies don’t pay, the Cuba group will threaten to dump sensitive files on a website they have been operating on the dark web since January this year.
Security Friday: News and Apple Watch Tips – TMO Daily Observations 2021-10-22
Andrew Orr joins host Kelly Guimont to discuss Security Friday news and updates on ransomware and hacking, and share how your Watch can make you safer.
'REvil' Ransomware Group Taken Down Through Multi-Country Effort
The FBI, working with Cyber Command, the Secret Service, and other countries, took down REvil.
According to three people familiar with the matter, law enforcement and intelligence cyber specialists were able to hack REvil’s computer network infrastructure, obtaining control of at least some of their servers. After websites that the hacker group used to conduct business went offline in July, the main spokesman for the group, who calls himself “Unknown,” vanished from the internet.
Ransomware Attack on Sinclair Broadcasting Linked to Russian Group 'Evil Corp'
Last weekend, Sinclair Broadcast Group found itself the victim of a ransomware attack, and sources claim Russian group Evil Corp. was behind it.
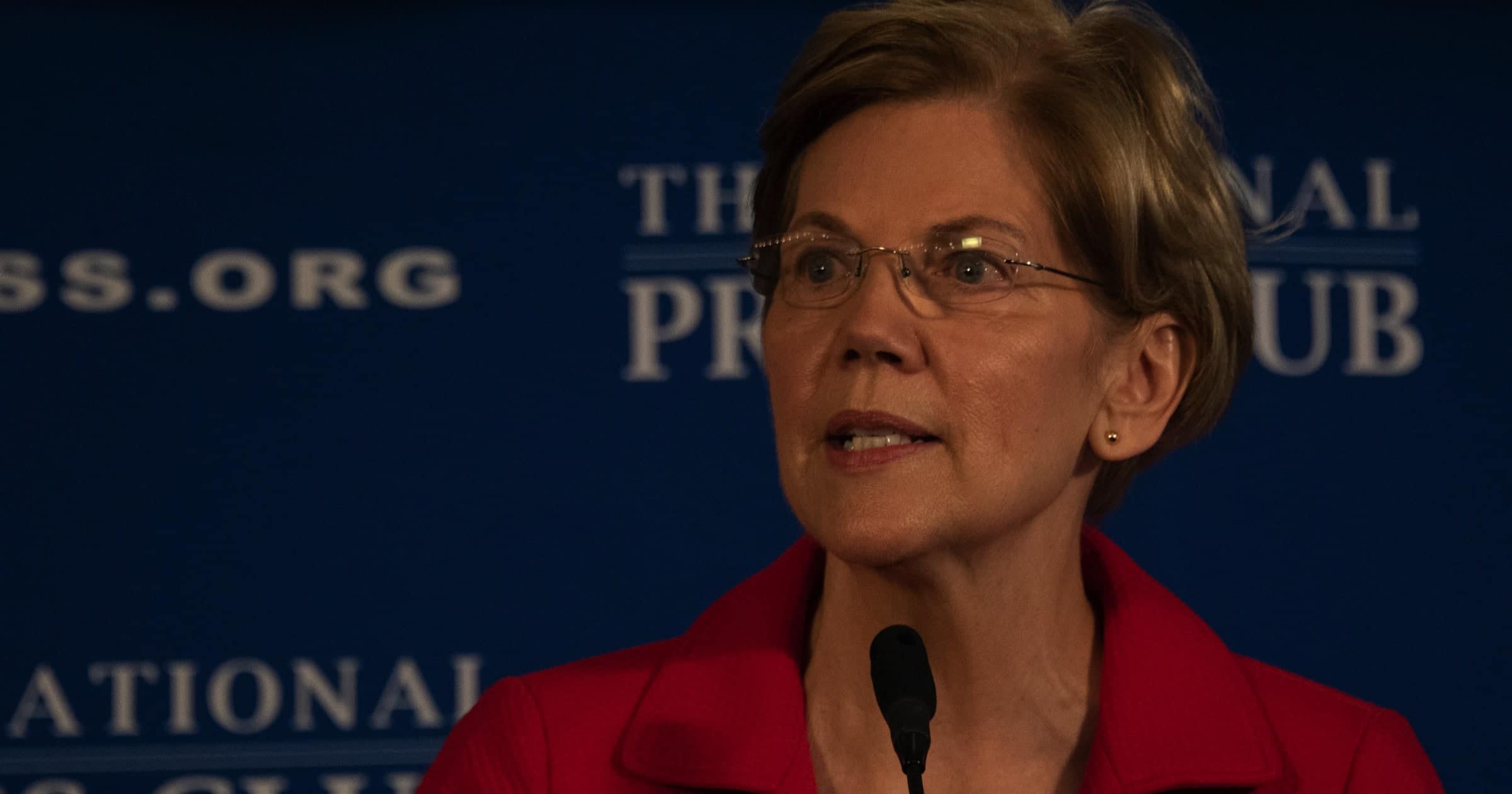
Proposed Bill Would Require Disclosures of Ransomware Payments
Under the Ransom Disclosure Act, victims of ransomware who pay their attackers would have to report the payment within 48 hours.
Backblaze Announces Disaster Recovery Solution for Backups
Backblaze has announced “Backblaze Instant Recovery in Any Cloud” on Tuesday. It’s aimed at ransomware attacks so affected companies can recover faster.
Security Friday: Bad, Real Bad, and Good News – TMO Daily Observations 2021-09-23
Andrew Orr joins host Kelly Guimont for a round of Security Friday news, including ransomware, hacking, and a way to protect your Apple Card.
Grain Cooperative 'New Cooperative Inc' Hit with BlackMatter Ransomware Attack
Cyber gang BlackMatter has attacked Iowa-based grain cooperative New Cooperative Inc with ransomware, successfully shutting down its systems.
The attack occurred on or around Friday, according to Allan Liska, senior threat analyst at the cybersecurity firm Recorded Future Inc. The ransomware gang, which goes by the name BlackMatter, is demanding a $5.9 million ransom, Liska said.
New Cooperative confirmed that they had been attacked and said they had contacted law enforcement and were working with data security experts to investigate and remediate the situation.
US Forms Joint Cyber Defense Collaborative to Fight Ransomware
CISA is forming an initiative called the Joint Cyber Defense Collaborative along with certain private sector companies such as Google and Microsoft.
DIY Automation, CarPlay, RAID, and More! — Mac Geek Gab 882
Sometimes the easy way isn’t the fun way, and this week we’ve got lots of do-it-yourself solutions to share from all of you. Listen as John and Dave share your ideas about automation, launch agents, CarPlay, drive arrays and much more. Of course, it wouldn’t be MGG without your two favorite geeks sharing Quick Tips, Cool Stuff Found, and their answers to all your other questions, would it? Listen, learn five new things, and don’t get caught!
Security Friday: News Old and New, and Future Updates – TMO Daily Observations 2021-07-16
Andrew Orr joins host Kelly Guimont to discuss updates to previous Security Friday news, and a couple of items coming to Firefox and iOS.
Charlotte Henry on DTNS - 'Where Have All The Ransoms Gone?'
The Mac Observer’s Charlotte Henry joined the DTNS crew on Monday. Amongst other things, they discussed paying ransoms following a ransomware attack, the combined theater and streaming released of Black Widow by Disney, and the future of the iPad mini.
JBS USA Pays $11 Million in Ransom After Cyberattack
On Thursday, meat supplier JBS said it paid US$11 million after ransomware attack stopped its operations.
In consultation with internal IT professionals and third-party cybersecurity experts, the company made the decision to mitigate any unforeseen issues related to the attack and ensure no data was exfiltrated.
I wonder if the FBI will recover this ransom as well, like the Colonial Pipeline money.
Fujifilm Fights Ransomware Attack and Works to Restore Servers
Fujifilm was hit by a ransomware attack last week but refuses to pay the ransom. Instead, it’s working to restore its servers with backups.
On 4 June it confirmed a ransomware attack was affecting a “specific network” in Japan and that it shut down “all networks and server systems” while it investigated the “extent and scale” of the attack.
Fujifilm said it would not comment on the amount demanded by the ransomware gang. The company has started bringing its network, servers, and computers in Japan “back into operation” and is aiming to be fully up and running “this week”. It has also restarted some product deliveries, which were particularly hard hit by the cyberattack.