The FBI is warning that an Eastern European cybercriminal group is mailing USB drives filled with BadUSB malware to various companies (via Bleeping Computer).
BadUSB Attacks
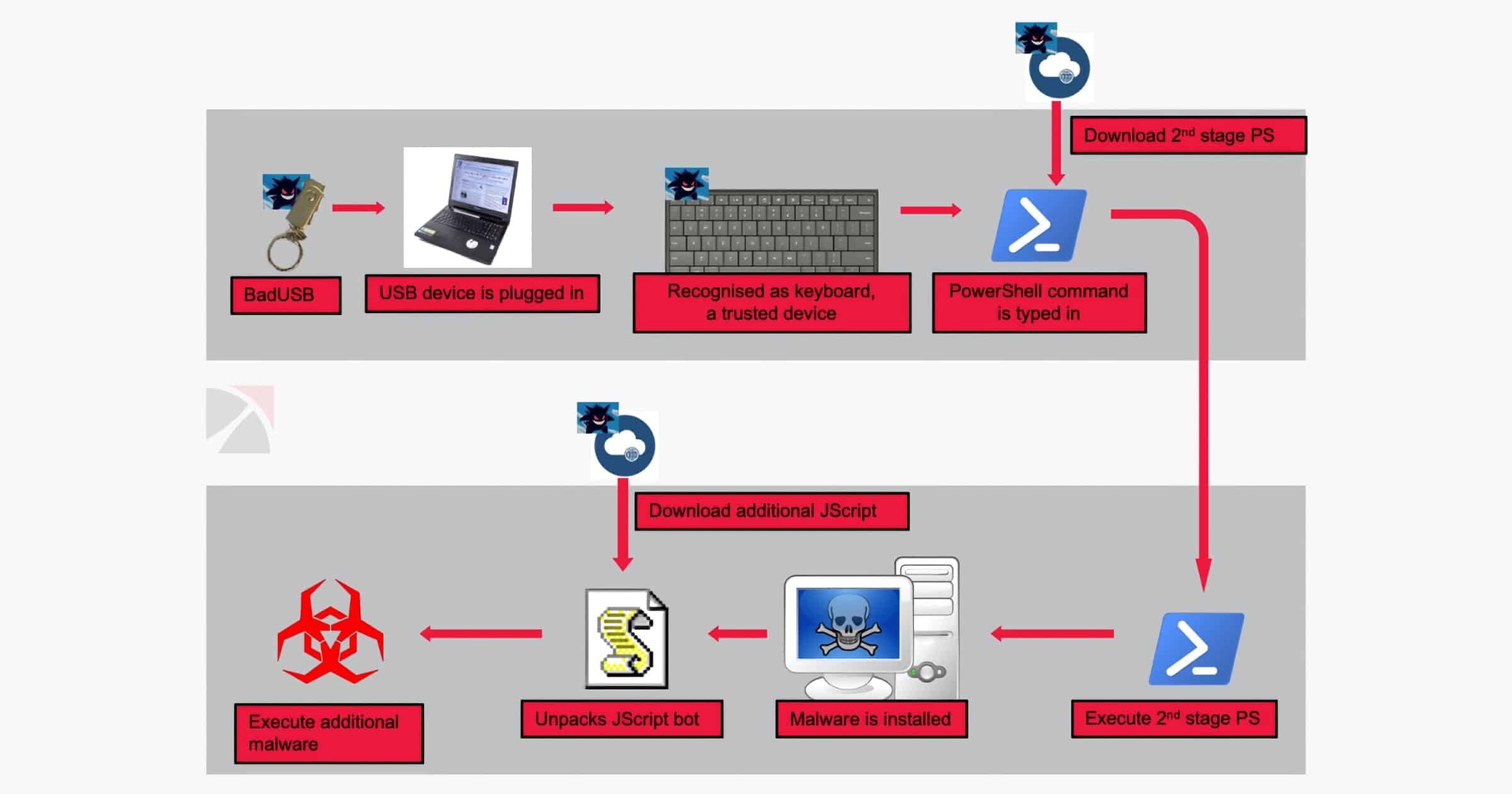
First demonstrated at the 2014 Black Hat conference, BadUSB adds malicious code to a device’s firmware. It can emulate a keyboard to type commands, act as a keylogger to record what you type, install malware, redirect network traffic, and more.
These USB drives were sent through USPS and UPS to unnamed companies in transportation and insurance since August 2021, and defense companies since November 2021. In some instances, the package contained a letter pretending to be from the U.S. Department of Health and Human Services with a COVID-19 warning. In other cases, the package purports to be from Amazon and includes a gift card alongside the USB drive. The hope is that BadUSB could drop ransomware into the company’s network.
The FBI is saying that FIN7 is responsible for the packages. This group is blamed for billions of dollars in losses to consumers in businesses, both in the U.S. and other countries. The Department of Justice accused the group of stealing credit card numbers from restaurants and hospitality businesses in 47 states. They impersonated Best Buy and mailed similar packages to these companies in 2020.
Of course, the BadUSB attack can easily avoided by not plugging in random USB drives into your computer. Companies can also lock down their machines or require an employee ID to use a USB drive on their computer. So if you receive a USB drive in the mail that you weren’t expecting, don’t plug it in!