Apple just added an important security feature for iMac Pro users, one that allows users to precisely control which storage devices are allowed to boot up their Macs. It’s called Startup Security Utility, and it allows users to designate allowed boot drives and require a password to change that. This will, in theory, stop someone from using their own boot drive to access, copy data from, or install malware or keyloggers on an iMac Pro.
The key phrase, though, is iMac Pro, as Startup Security Utility is currently “available only on iMac Pro.” As of this writing, there’s no indication on whether this feature will be rolled out to other Mac models in the future, though it’s a reasonable guess Apple’s next Mac Pro will feature this or a similar technology.

Startup Security Utility
Apple’s new Startup Security Utility has three components: Firmware password protection, Secure Boot, and External Boot. Each offers different levels of granular control over how an iMac Pro can be booted up.
Firmware Password
The base level of control in Startup Security Utility is Firmware Password. Apple positioned this as a step beyond filevault, one that requires a password to use any bootup storage device other than one’s designated startup disk. From Apple’s description [emphasis added].
A firmware password prevents users who don’t have the password from starting up from any disk other than your designated startup disk. As a result, it also blocks the ability to use most startup key combinations.
Firmware Password also works alongside Lost Mode in Find My Mac. According to Apple, “Lost Mode works even while using a firmware password. Unlike the passcode set by Lost Mode, a firmware password remains on until you turn it off with Firmware Password Utility.”
Apple has a dedicated KnowledgeBase article for setting up a Firmware Password.
Secure Boot
Secure Boot tackles startup security from a difference angle by allowing users to ensure their iMac Pro starts up only from a, “legitimate, trusted operating system.” It does so with three levels of security: Full Security, Medium Security, and No Security. The screenshot below shows those options.
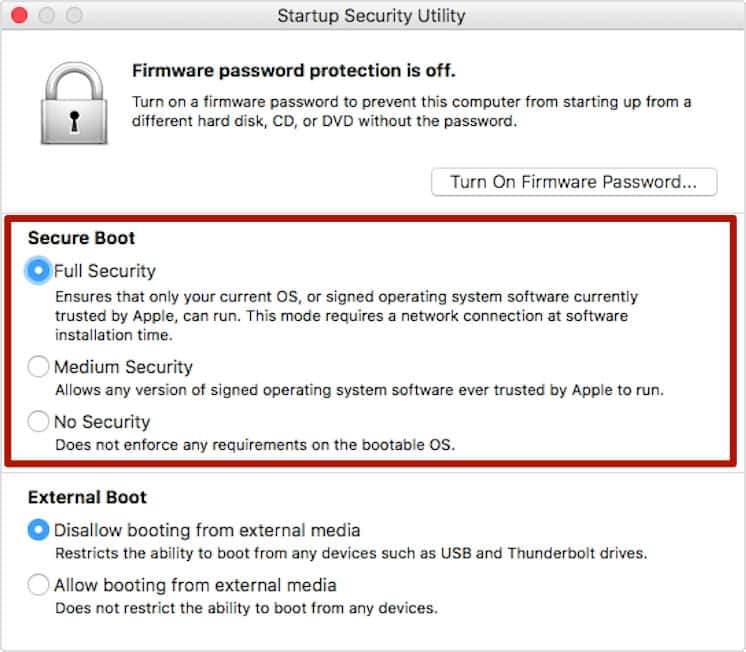
Below, we have descriptions of each option.
Full security:
During startup, your Mac verifies the integrity of the operating system (OS) on your startup disk to make sure that it’s legitimate. If the OS is unknown or can’t be verified as legitimate, your Mac connects to Apple to download the updated integrity information it needs to verify the OS. This information is unique to your Mac, and it ensures that your Mac starts up from an OS that is trusted by Apple.
Medium Security:
During startup when Medium Security is turned on, your Mac verifies the OS on your startup disk only by making sure that it has been properly signed by Apple (macOS) or Microsoft (Windows). This doesn’t require an Internet connection or updated integrity information from Apple, so it doesn’t prevent your Mac from using an OS that is no longer trusted by Apple.
No Security:
The No Security setting doesn’t enforce any of the above security requirements for your startup disk.
External Boot
The third security option in Startup Security Utility is External Boot.
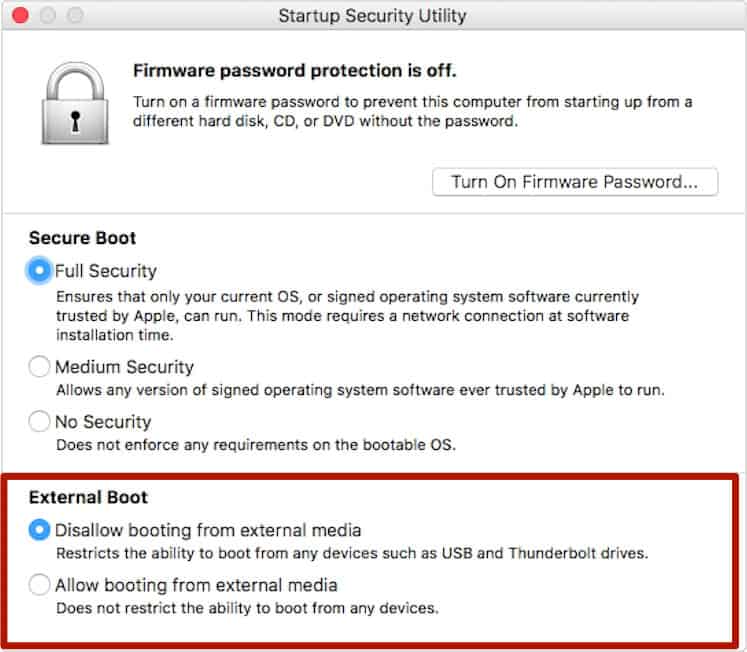
From Apple:
Use this feature to control whether your Mac can start up from an external hard drive, thumb drive, or other external media. The default and most secure setting is ”Disallow booting from external media.” When this setting is selected, your Mac can’t be made to start up from any external media.
This option would prohibit you or anyone else from booting your iMac Pro up from any external media under any circumstances (other than having access to your designated startup disk and changing the option there.) That might well be important for users with highly sensitive data and/or iMac Pros operating in unsecure locations, but it could mean trouble if something happens to your designated startup disk.
My reading of this feature is that not even knowing the Firmware Password would allow you to boot an iMac Pro from external media. At all.
Security as a Feature
All in all, Startup Security Utility is a significant boost for iMac Pro, and one that could be particularly valuable in sensitive enterprise, defense industry, and other government uses. I hope it gets rolled out to future Macs, as well/

It wasn’t clear in the article that Firmware Password has been around for over a decade. I thought it might be nice to point that out in case people want some of this security now.
The Startup Security Utility uses the Mac Pro’s ARM CPU to startup the Mac Pro and maintain security. Only Macs with ARM CPUs will be able to use this feature. I assume every new Mac will have an ARM CPU to maintain security, run Face ID and Touch ID. This Apple Custom ARM CPU with a Secure Enclave would also make it difficult to clone a Mac in the future.
Only if future versions of the OS require the Secure Enclave or other related hardware. (This is the opposite – making sure the OS isn’t a “clone”.) That said, the DIY clone market is SO small, I am doubtful Apple will go that far. They haven’t yet. So far, they’ve only gone after the companies that are trying to make money off of their IP.