Security researcher Patrick Wardle found a Safari adware extension called GoSearch22 has been rewritten to target M1 Macs. It has been detected in the wild.
GoSearch22
Part of the Pirrit Mac adware family, GOSearch22 was originally created with Intel x86 chips in mind. But as the Mac transitions to Apple silicon malware authors set their sights on the new ARM-based (arm64) chip.
When users have apps like GoSearch22 installed on a browser and/or the operating system, they are forced to occasionally see coupons, banners, pop-up ads, surveys, and/or ads of other types. Quite often ads by apps like GoSearch22 are designed to promote dubious websites or even download and/or install unwanted apps by executing certain scripts. Moreover, adware-type apps like GoSearch22 tend to be designed to collect browsing data.
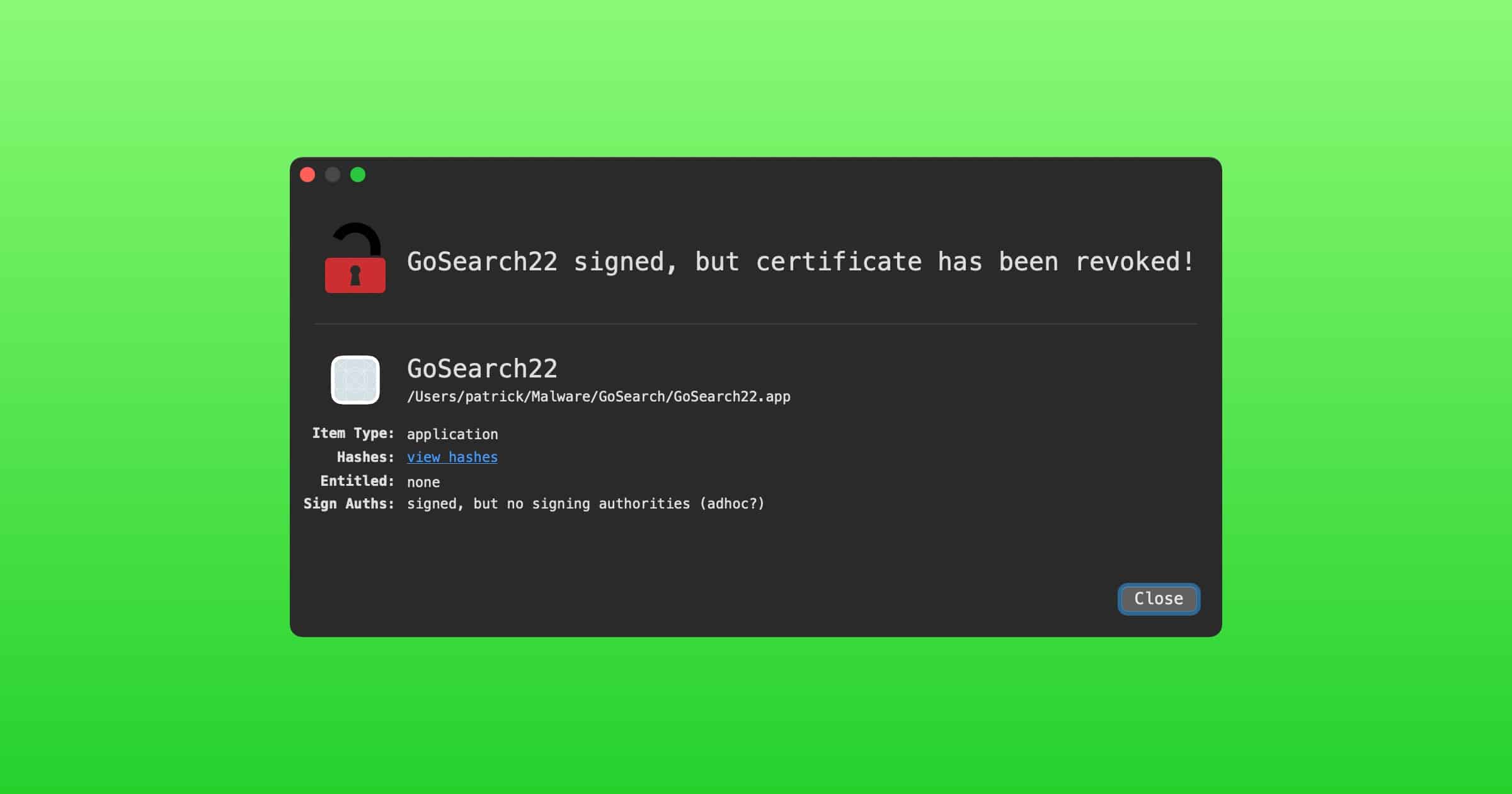
Interestingly, GoSearch22 was signed by an Apple developer ID (hongsheng tan) on November 23, 2020. But Mr. Wardle wasn’t able to determine if the code was notarized by Apple, because Apple had revoked the developer’s certificate already. In August 2020, for example, Apple accidentally notarized a piece of Mac malware called OSX.Shlayer.
It’s highly likely in the future we’ll see more examples of M1 malware.