On Monday, police in Europe announced the arrests of over 100 people connected to the Mafia. They were using hackers to support efforts in traditional crime.
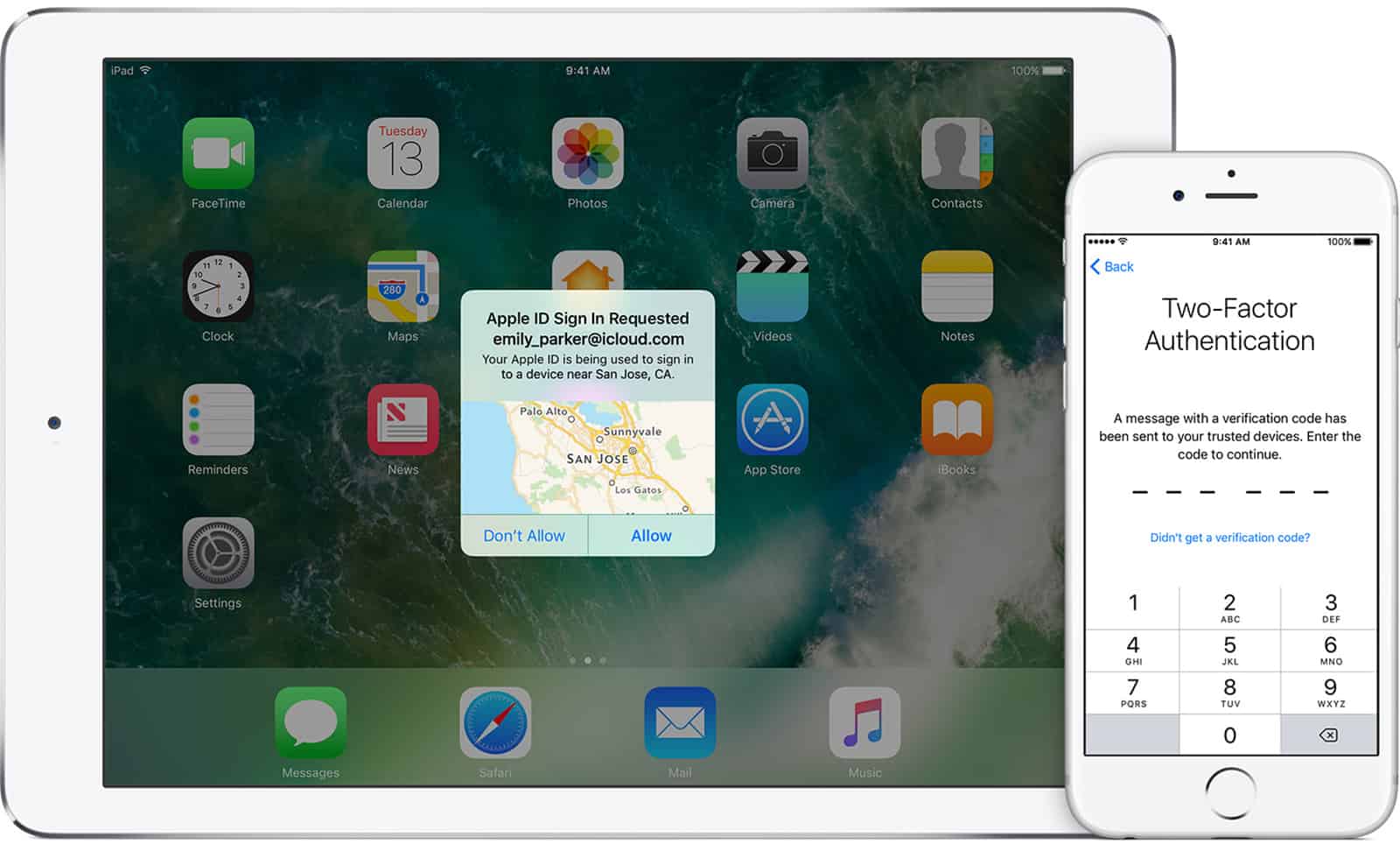
The authorities said that the organized crime groups employed hackers who were using phishing, social engineering attacks, and SIM swapping, as well as sending malware to victims with the goal of taking over their bank accounts and stealing their money.
This operation highlights a new trend: traditional organized crime groups, such as the Italian Mafia and Camorra, are now dabbling in cybercrime to support their traditional offline activities, according to Italian and Spanish police investigators involved in the crackdown who spoke with Motherboard.