An urgent update to the Zoom client for your Mac addresses a serious vulnerability. Install it now to keep your Mac free of malware.
zoom
[U] Remotion Delivers a New Way to SharePlay Spotify
Spotify has announced Remotion, a client for macOS users that allows users to stream music from Spotify while making audio/video calls.
Update Zoom to Stop Your Mac's Mic Staying Active After a Call
A Zoom update appears to fix a bug that stopped a Mac’s mic from being disabled after a meeting had ended.
Zoom Tests Advertising for Users on Free Plan
Zoom announced on Monday that it will begin piloting advertising for users on the free Basic plan.
For this initial program, ads will be rolled out only on the browser page users see once they end their meeting. Only free Basic users in certain countries will see these ads if they join meetings that are hosted by other free Basic users.
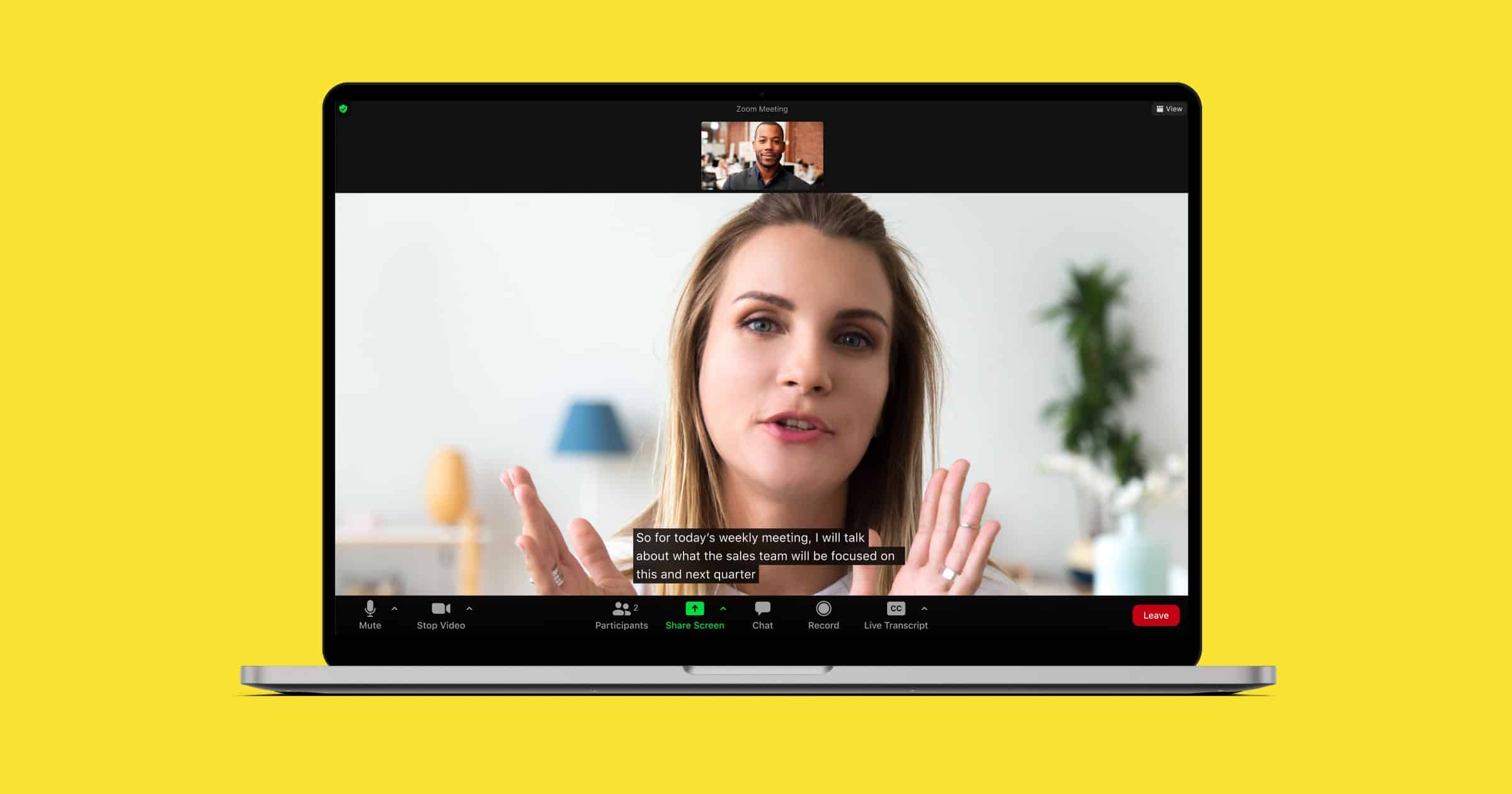
Zoom Updates for M1 MacBook Pro With Auto-Generated Captions
Zoom announced new features aimed at helping business communications and remote workers. The app has been optimized for the 2021 MacBook Pro.
Zoom, Also Email Horrors – TMO Daily Observations 2021-10-06
Charlotte Henry joins host Kelly Guimont to discuss a quick Zoom tip, and a (seasonal) story about the horrors of an overstuffed inbox.
How To Force Zoom to Quit When It Won’t Shut Down
While Zoom is normally a fairly well-behaved app that closes when it should, sometimes it gets stuck. Jeff Butts walks you through how to use Terminal commands to force Zoom to quit when it simply won’t.
Zoom to Pay $85 Million Over Encryption, Sending User Data
Zoom is paying US$85 to settle claims that it lied about offering end-to-end encryption, as well as giving users data to Facebook and Google.
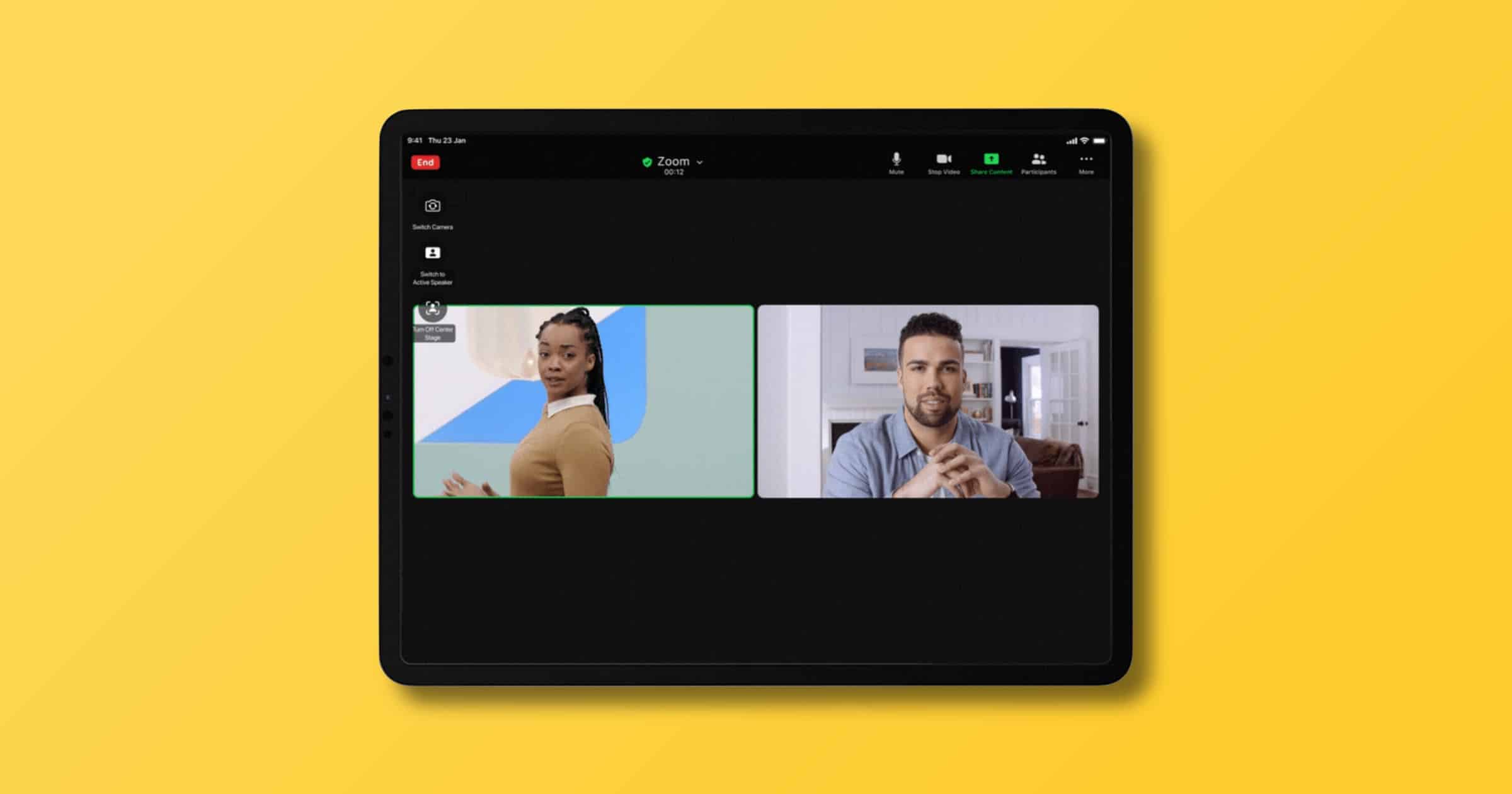
Zoom Announces Support for 2021 iPad Pro ‘Center Stage’
On Wednesday Zoom announced that its app will add support for the 2021 iPad Pro’s Center Stage feature that uses the device’s wide angle camera.
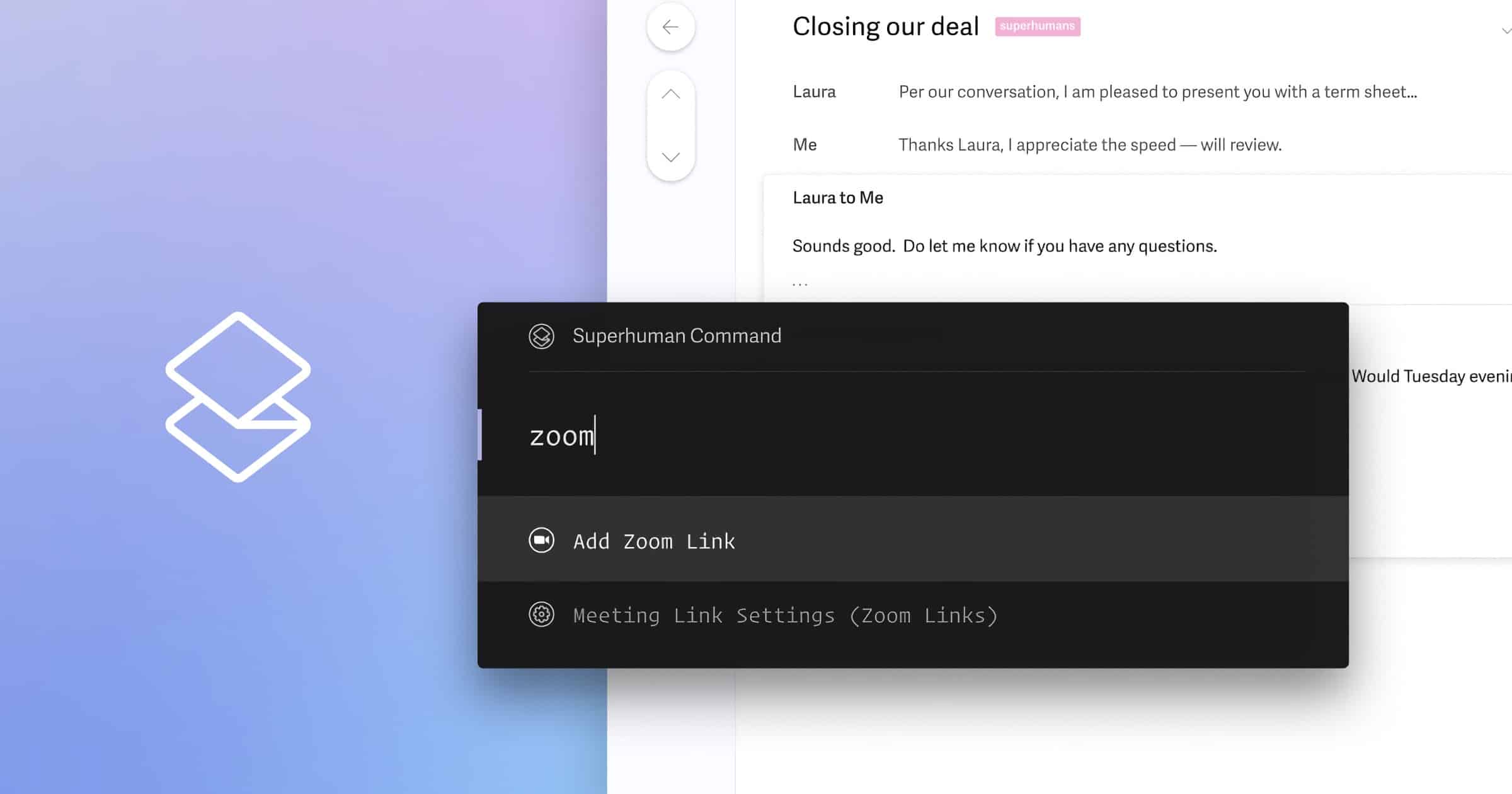
Superhuman Email Rolls Out Support for Zoom, Google Meet
Email app Superhuman is rolling out support for Zoom and Google Meet integrations into its calendar. The integration was one of the most highly requested features from Superhuman users. With the new integration, users will be able to add Zoom or Google Meet links to the calendar events they create in Superhuman. Like the rest of the calendar experience – you’ll be able to do so with the keyboard only. Superhuman mail is a US$30/month subscription.
How to Change Your Zoom Display Name
As usernames replace nametags, you may want to change your Zoom display name so that, for example, people can see which company you are from.
DOJ Charges Zoom Executive With Aiding Chinese Government
The Department of Justice is charging a China-based Zoom executive with aiding the Chinese government to shut down certain Zoom meetings.
Zoom Rolls Out End-to-End Encryption for Video Calls
Starting next week, video conferencing app Zoom is finally adding end-to-end encryption to its platform.
Zoom’s E2EE offering uses public key cryptography. In short, the keys for each Zoom meeting are generated by participants’ machines, not by Zoom’s servers. Encrypted data relayed through Zoom’s servers is indecipherable by Zoom, since Zoom’s servers do not have the necessary decryption key. This key management strategy is similar to that used by most end-to-end encrypted messaging platforms today.
Good to see Zoom doing this; they’ve certainly had misses in the past. Update: The new version is now available for most users.
Security Friday, New iPhone Prepping – TMO Daily Observations 2020-10-16
Andrew Orr joins host Kelly Guimont for Security Friday news, The Week In Data Breaches, and tips for a seamless transfer to a new iPhone.
Glenn Fleishmann Introduces Free Book ‘Take Control of Zoom Essentials’
Glenn Fleishman has released a free version of his book called “Take Control of Zoom Essentials” as well as updated the paid version called “Take Control of Zoom”. Take Control shared the news in a blog post:
Yesterday, we released two Zoom-related books by Glenn Fleishman: a new, free book called Take Control of Zoom Essentials and a gigantic version 1.1 update to the comprehensive Take Control of Zoom. We know a lot of people are using Zoom for work and school, and we hope you find these books helpful.
Zoom usage has skyrocketed now that more people have been working and learning from home due to the COVID-19 pandemic. Consider these books to know everything you want to know about using the video sharing platform.
Zoom Backtracks, Will Give Free Users Encryption Protection
After a lot of negative attention from press and privacy advocates, Zoom has backtracked on its stance. It will provide free users with end-to-end encryption, a feature previously limited to paying customers.
The company said that free users will have to verify themselves with a phone number in a one-time process. It claimed that this will stop bad actors from creating multiple abusive accounts.
Zoom is also releasing an updated design of its end-to-end encryption solution on GitHub that intends to achieve a balance between “the legitimate right of all users to privacy and the safety of users.”
Good to see Zoom do this.
U.S. Lawmakers Ask Zoom About its Ties to China
Three lawmakers in the U.S. have asked Zoom to clarify its relationship with China after the company suspended user accounts at its request.
Zoom Purchases End-to-End Encryption Specialist Keybase
Zoom is buying security firm Keybase in order to help the video-conferencing firm implement end-to-end encryption.
Zoom Security Tips – TMO Daily Observations 2020-04-28
Charlotte Henry joins host Kelly Guimont to discuss newly everywhere meeting service Zoom, and how hosts and attendees can stay safe.
Zoom: How to Host a Meeting Safely
300 million people a day use Zoom. You’re probably one of them. Here are some tips on how to host a meeting on it safely.
Zoom Account Credentials Are Being Sold Across Hacker Forums And The Dark Web
Credentials for at least half-a-million Zoom accounts have been sold across the dark web and hacker forums for negligible amounts of money.
Zoom: Don’t Want to Get Routed Through Chinese Servers? Fork Over Your Cash
One of Zoom’s controversies is how it routes some of its network traffic through China’s servers. If you’re privacy conscious, you can opt out of specific data center regions starting April 18. But this is only for paying customers.
This feature gives our customers more control over their data and their interaction with our global network when using Zoom’s industry-leading video communication services.
I can’t say I agree. It’s not about making privacy a paid feature, it’s that Zoom is exploiting its own insecurity to create a paid feature. Next step: Making end-to-end encryption a paid feature, and leaving free users to fend for themselves.
Zoom’s Encryption is Linked to Chinese Servers
Researchers found that Zoom uses its own encryption scheme, sometimes using keys issued by China.
Some of the key management systems — 5 out of 73, in a Citizen Lab scan — seem to be located in China, with the rest in the United States. Interestingly, the Chinese servers are at least sometimes used for Zoom chats that have no nexus in China. The two Citizen Lab researchers, Bill Marczak and John Scott-Railton, live in the United States and Canada. During a test call between the two, the shared meeting encryption key “was sent to one of the participants over TLS from a Zoom server apparently located in Beijing,” according to the report.
I don’t have further commentary on Zoom, other than asking, “How will this end?”
New Zoom Bug Can Be Used to Steal Passwords, Access Your Webcam, Microphone
Security researcher Patrick Wardle disclosed two Zoom bugs today. They can be used to steal Windows passwords and access your webcam and microphone. They do however require physical access to the machine.
In this blog post, we’ll start by briefly looking at recent security and privacy flaws that affected Zoom. Following this, we’ll transition into discussing several new security issues that affect the latest version of Zoom’s macOS client.
At this point, Zoom should just rewrite its software completely.
![[U: Play It Again, Sam] Update Zoom On Your Mac Now: Vulnerability Could Give Attacker Full Access to Your Computer](https://www.macobserver.com/wp-content/uploads/2022/08/zoom-update-vulnerability.jpg)
![[U] Remotion Delivers a New Way to SharePlay Spotify](https://www.macobserver.com/wp-content/uploads/2022/07/SpotifyRemotionJuly2022Featured.jpg)