EyeQue’s new AR-powered vision app, MyReaderNumber, lets people take vision tests for near-vision and mid-distance vision.
Articles by Andrew Orr
Boost and Breach Insurance Partner on Crypto Wallet Insurance
Boost Insurance and Breach Insurance are partnering to launch the first-ever crypto wallet insurance product. It’s called Crypto Shield.
OpenSea and CoinTracker Want to Help With NFT Taxes
Do you need help with your NFT taxes? Good news, OpenSea and CoinTracker are teaming up to help consumers.
New York Attorney General Warns of Malicious AirTag Tracking
New York Attorney General Letitia James issued a consumer alert to warn New Yorkers of malicious AirTag tracking.
New Chrome OS Flex Could Revive Your Old Mac
Google has introduced Chrome OS Flex, its project that lets individuals, schools, or businesses put Chrome OS on their aging machines.
Totallee Hybrid MagSafe Cases Released for iPhone 12
Hybrid MagSafe cases for the iPhone 12 series are available from totallee for US$39. In December these cases were released for the iPhone 13.
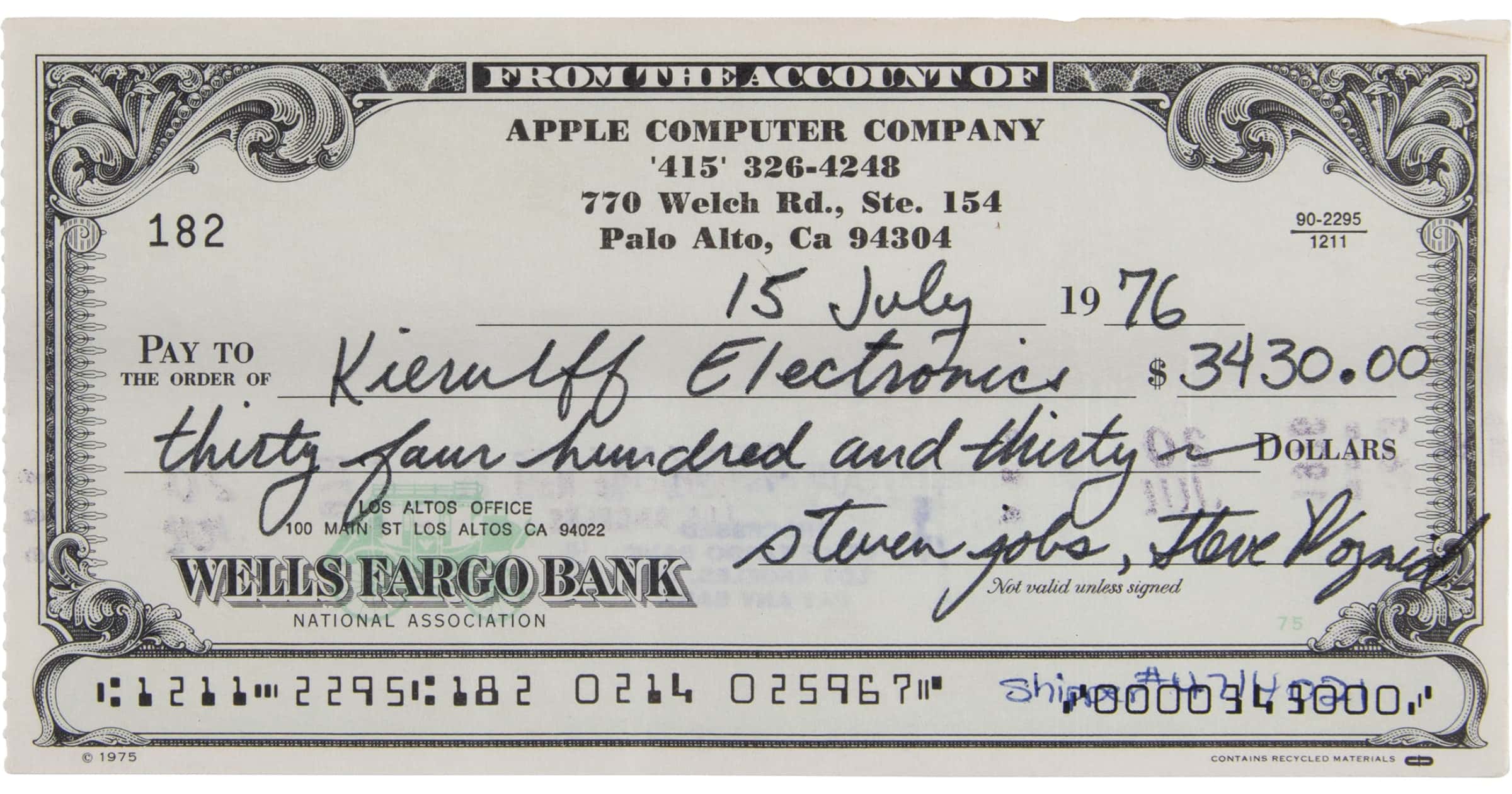
New Apple Auction Includes Items From Steve Jobs, Doug Engelbart, With Atari Application
RR Auction is presenting a new auction, one that is themed called “The Steve Jobs Revolution: Engelbart, Atari, and Apple.”
GiveSendGo Data Breach Affects Donors of 'Freedom Convoy'
Attackers have breached the systems of GiveSendGo, a Christian fundraising platform. People who donated to the Freedom Convoy in Canada.
Apple Music Replay 2022 Playlist Now Available
The Apple Music Replay 2022 playlist is now available for subscribers to peruse. It’s a fun way to see which songs you played the most.
BBEdit 14.1 Update Adds Support for Shortcuts on Mac
BBEdit 14.1 is out on Tuesday and adds support for Shortcuts, an expanded notes system, and a new image viewer.
'BackPack' iMac Shelf Can Hold Accessories on Your Stand
Twelve South has a new BackPack iMac shelf. It comes in different colors to match your device so you can display accessories
Missouri Backs Away From 'View Source' Hacking Prosecution
A Cole County prosecutor has declined to prosecute reporter Josh Renaud over claims that he hacked into the state’s website.
BlockFi Pays $100 Million Penalty to SEC Over Crypto Lending Product
The SEC has penalized BlockFi US$100 million after it failed to register high-yield interest accounts as securities.
FBI: BlackByte Ransomware Attacks Critical Infrastructure
The FBI and Secret Service have seen signs of BlackByte ransomware attacking at least three critical infrastructure sectors in the U.S.
Texas Sues Meta Over Facebook Facial Recognition
Texas Attorney General Ken Paxton filed a lawsuit against Meta. It seeks civil penalties due to Facebook’s facial recognition practices.
Appointment Booker 'FlexBooker' Suffers Second Data Leak
The vpnMentor research team discovered a data leak from FlexBooker, a company that makes online appointment booking tools for businesses.
FBI Flash Report Warns of Attacks With LockBit 2.0 Ransomware
The FBI has issued a flash report this week that details indicators of compromise (IOC) linked to LockBit 2.0 ransomware.
Senators Reveal CIA Program That Collects American Data
According to two Democrats on the Senate Intelligence Committee, the CIA has an undisclosed repository of data collected from Americans.
Western Digital NAND Contamination Leads to 6.5 Exabytes in Losses
Due to contamination issues with its NAND production, Western Digital Corp says it has lost approximately 6.5 exabytes of flash storage.
iOS 15.3.1 Fixes an Issue With Braille Displays Not Working
Apple has released iOS 15.3.1 on Thursday that that fixes a problem with an accessibility feature. It also contains security fixes.
Here's How Apple Will Work to Fight AirTag Stalking
Apple released a report on Thursday about its plans to fight AirTag stalking through software updates in the future.
These Experts Have a Vision for the Internet in 2035
Have you ever wondered about the internet in 2035? A report from Pew Research Center shares what experts believe.
iPhone 13 Comparison Against the Samsung Galaxy S22
How does Apple’s latest smartphone compete with the Samsung Galaxy S22? PCMag published this iPhone 13 comparison to find out.
Review: Polarr is a Flexible Photo Editor for Many Platforms
Polarr is a photo-editing app for iOS and Android that packs a punch. It has a lot of features for people to edit and create/share styles.