Google Chrome seems to be working on “quick delete” feature for iOS users, after announcing the feature on Android devices a while back.
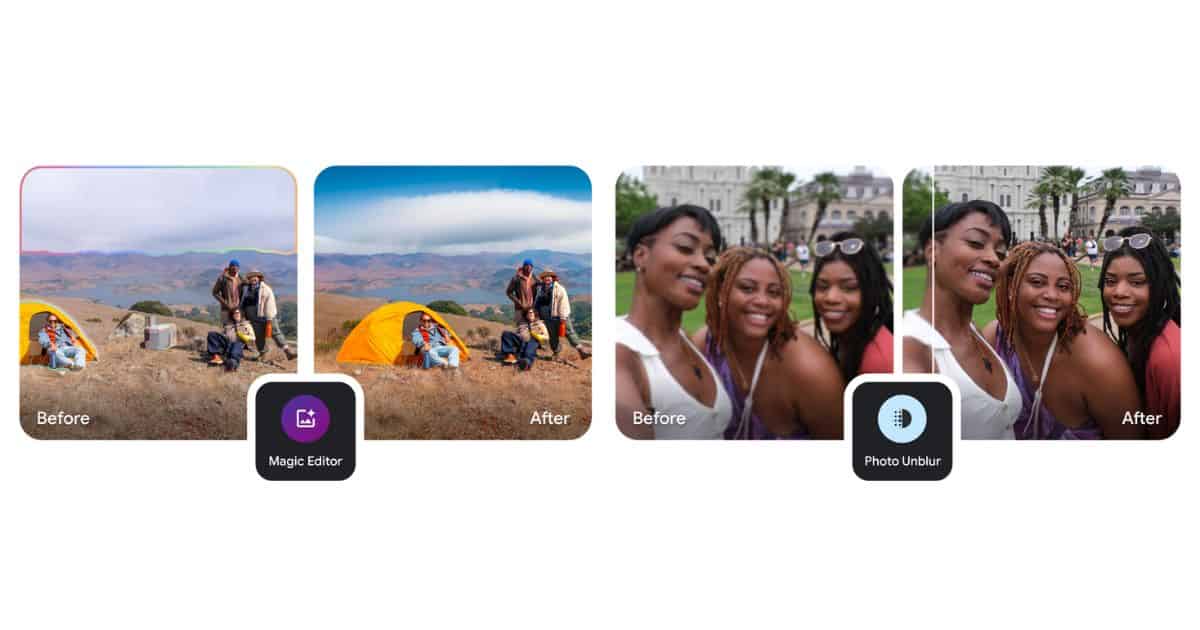
Google Photos Is Bringing Magic Editor to iPhones & iPads Soon
Google is launching Magic Editor, earlier exclusive to Pixel 8 series and Google One subscribers, on Android and iPhone, starting May 15.
Google Chrome for iPad Will Soon Let You Group Multiple Tabs
Google Chrome for iPadOS might be getting the option to group tabs soon, coming hot on the heels of the successful debut on PC and Android.
Google Chrome for iOS Now Has a Native Package Tracking Feature
The new tab page on the latest version of Chrome on iOS can now track your packages.
How to Block Temu.com Ads on iPhone | Full Guide
Learn how to block Temu.com and its intrusive ads on Google, Safari, and iPhone using personalized settings, ad-blockers, and VPNs.
iPhone 14 Plus Fails at Failing - TMO Daily Observations 2023-03-22
Since its introduction, most in the tech press have deemed iPhone 14 Plus a failure. New numbers indicate otherwise, leaving most in the tech press to question how Apple got it so wrong? No. That doesn’t make sense. TMO writer Nick deCourville and Ken will discuss it. Plus – Google Bard goes bigger and a very convincing Steve Jobs chatbot.
Big Tech's Big A.I. Push with Tom Merritt - TMO Daily Observations 2023-02-10
Daily Tech News Show’s Tom Merritt named generative A.I. the most important story of 2022. It is not slowing down in 2023. He joins Ken to talk about this week’s announcements from Microsoft and Google. Plus – what’s going on with Apple and A.I.?
How to Double Space in Google Docs with an iPad
For those using Google Docs on an iPad, there’s a rather easy way to double space your text and paragraphs: here’s how.
Holding a Grudge and Loosening Restrictions - TMO Daily Observations 2023-01-26
Secret sources tell the Financial Times that Apple is trying to lessen its ties with Google over feelings of betrayal tied to Android. TMO Managing Editor Jeff Butts and Ken discuss why it’s a good article anyway. Plus – Rumor has Apple loosening its COVID policies. Yay?
Evercore Loves the M2, the DoJ Goes After Google and More
One financial type loves Apple’s M2, the DoJ goes after Google, and Apple ushers in Data Privacy Day. That’s today’s Observation Deck view.
Microsoft Looking Into 'Super App' to Directly Compete with Apple and Google in Search Engine Markets
Reports indicate that Microsoft may develop a “super app” that would compete in the search engine market alongside Google and Apple.
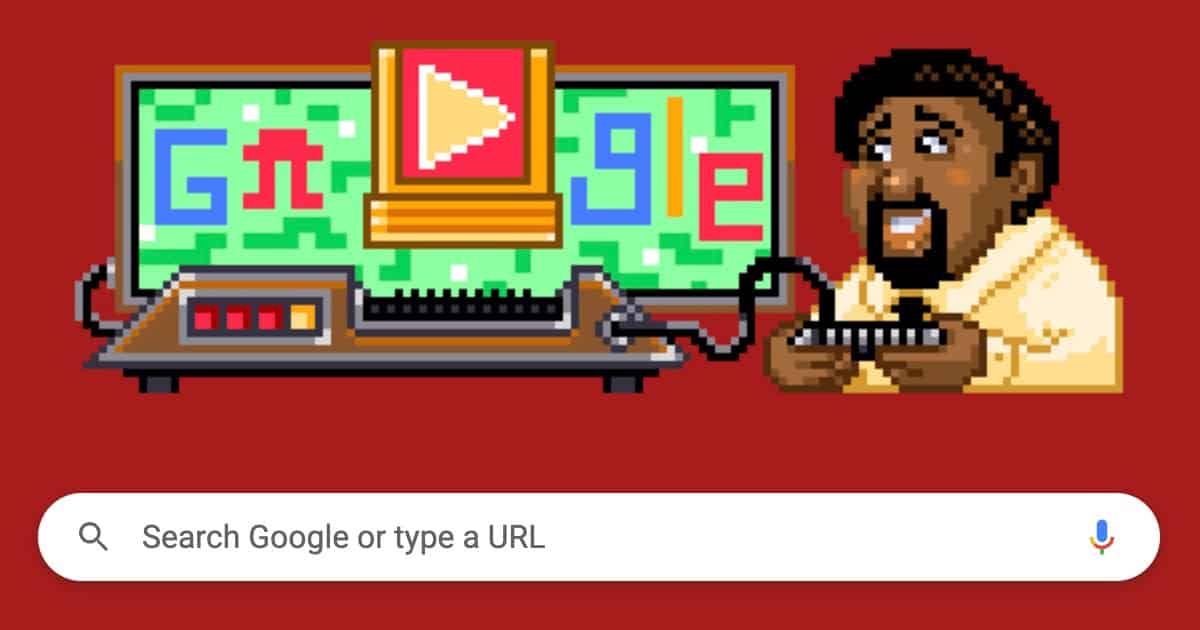
Google Doodle Allows Users to Create Their Own Game to Celebrate Life of Developer Jerry Lawson
A new Google Doodle now allows users to create their own games in celebration of the life and work of developer Jerry Lawson.
Google Is On the Hook for $392 Million in Largest-Ever US Consumer Privacy Lawsuit
Google has agreed to settle the largest consumer privacy lawsuit in the U.S. It’s agreed to pay out $392 million and change its practices.
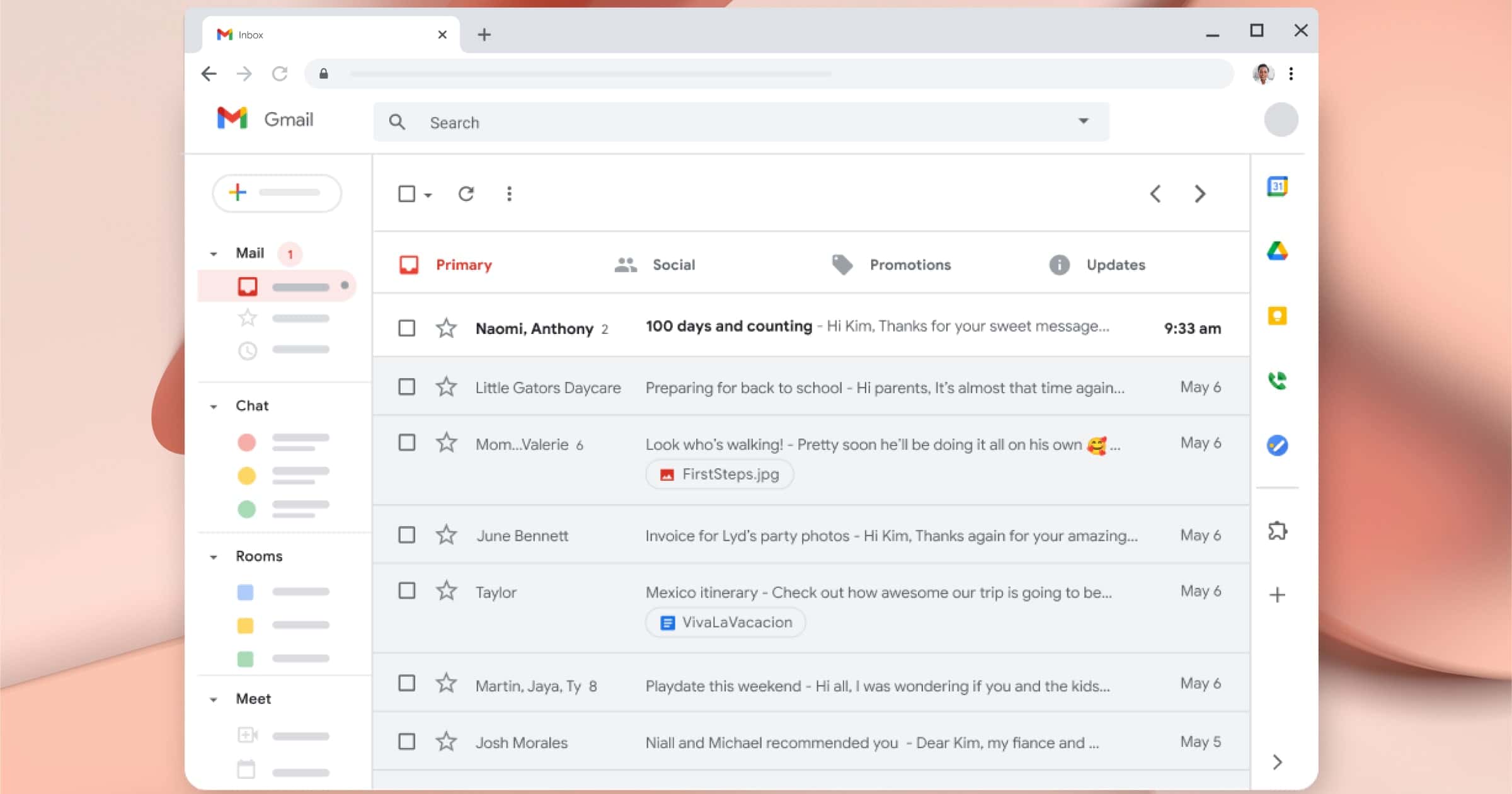
You Could See More Political Campaign Emails In Your Gmail Inbox
Thanks to an approved proposal from Google, you might see more political emails in your Gmail inbox this year than before.
Google Taps New Drake Song to Urge Apple into Adopting RCS for iMessage
In a tweet, Google poked fun at Apple not using RCS for Messages by taking a sample from Drake’s new song “Texts Go Green”.
Google TV App Arrives for iOS to the Apple App Store
Google TV is now available for iOS users. The new Google TV app replaces Google Play Movies & TV, much like it did on Android.
Google Russia Forced to Declare Bankruptcy
Google kept going in Russia, but it’s been rocky. Now, after facing a seizure of its bank account, Google Russia is filing for bankruptcy.
Apple Executive Ian Goodfellow Leaves Company to Rejoin Google
As Apple Executive Ian Goodfellow leaves the company due to its return-to-work policy, reports state the exec is returning to Google.
Civil Liberties Group Warns of Global Privacy Breach, Google Largest Offender
A civil liberties group warns of a global privacy breach that auctions personal user data. Google is one of the largest offenders.
Tech Giants Subject of ‘Monopolies Must Go’ Light Show Message in Washington, DC
A light show message insisting that “monopolies must go” will encourage Washington, D.C. commuters to write Congress about Big Tech bills.
Google and Android TV Lose Ability to Buy/Rent Movies in Apple TV App Update
The latest Apple TV app update for Google and Android removes the ability to buy and rent movies from iTunes on those devices.
Browser Makers Work on 'Interop 2022' for Compatibility
Apple, Mozilla, Google, and Microsoft are working on a benchmark called Interop 2022. It aims to help make developing for the web easier.
Android Announces Ad Privacy Changes, Takes Swipe at Apple
Google announced an overhaul in its approach to advertising and privacy on Android phones, and got in a swipe at Apple.
New Chrome OS Flex Could Revive Your Old Mac
Google has introduced Chrome OS Flex, its project that lets individuals, schools, or businesses put Chrome OS on their aging machines.