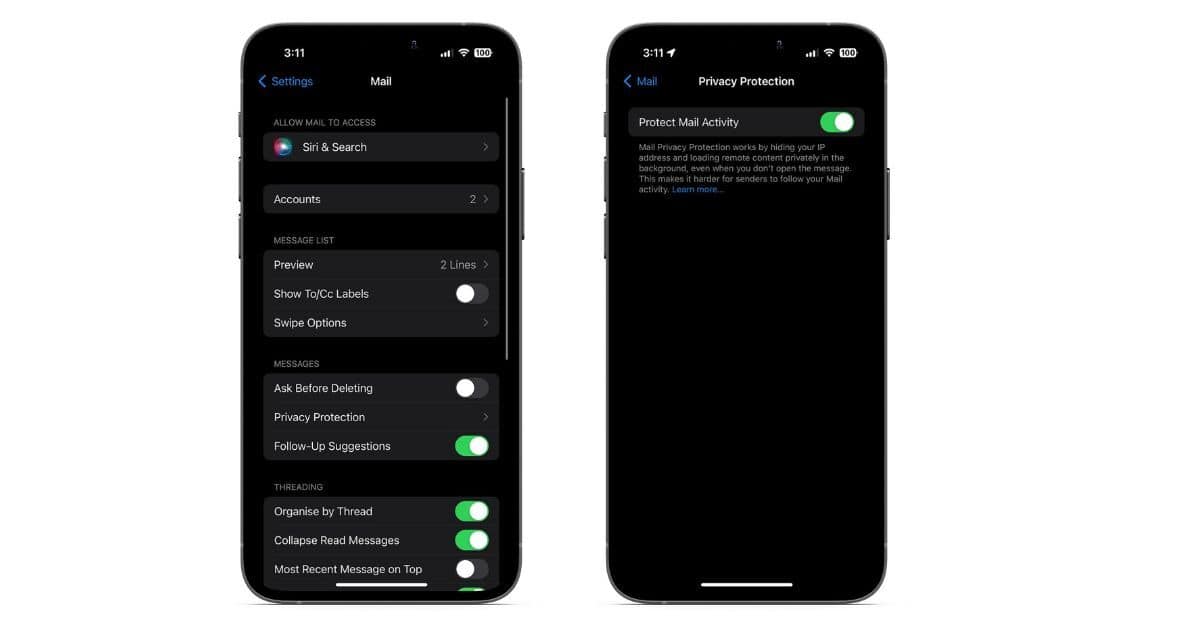
In this guide, we’ll help you learn more about Apple Mail Privacy Protection and how to enable and use it on your iPhone, iPad and Mac.
privacy
How to Delete Your Private Data from Apple's Servers
In order to delete your private data from Apple’s servers you need to delete your Apple ID. Alternatively can also learn how to deactivate it.
"Big Tech" as Bad Guy and a Touching Rumor - TMO Daily Observations 2023-01-12
POTUS thinks he’s found a cause to unify the left and the right in Congress: Fighting big tech. TMO writer Nick deCourville joins Ken to discuss President Biden’s WSJ call to arms. Then – A rumor about a touchscreen Mac on the horizon. Nick and Ken discuss the merits.
Google Is On the Hook for $392 Million in Largest-Ever US Consumer Privacy Lawsuit
Google has agreed to settle the largest consumer privacy lawsuit in the U.S. It’s agreed to pay out $392 million and change its practices.
A Privacy Lawsuit for Apple and the First Mailbag Monday - TMO Daily Observations 2022-11-14
Security researchers say Apple was/is tracking a lot of App Store activity in iOS 14.6. In the time of iOS 16.1.1, this has led to a lawsuit. TMO Managing Editor Jeff Butts and Ken talk that over. Plus – Twitter and Emergency SOS via Satellite and Steve Jobs’ sandals make it into Mailbag Monday!
Developers Find Apple May Be Tracking User Data on App Store Through iOS
Reports indicate that Apple may be tracking what a users taps on and interacts with in the official App Store, sending the data to Cupertino.
New 'OG App' Provides Instagram Alternative Without the Meta Clutter
Two developers have created an alternative to Instagram known as the OG App, which aims to remove the clutter found on the official Meta app.
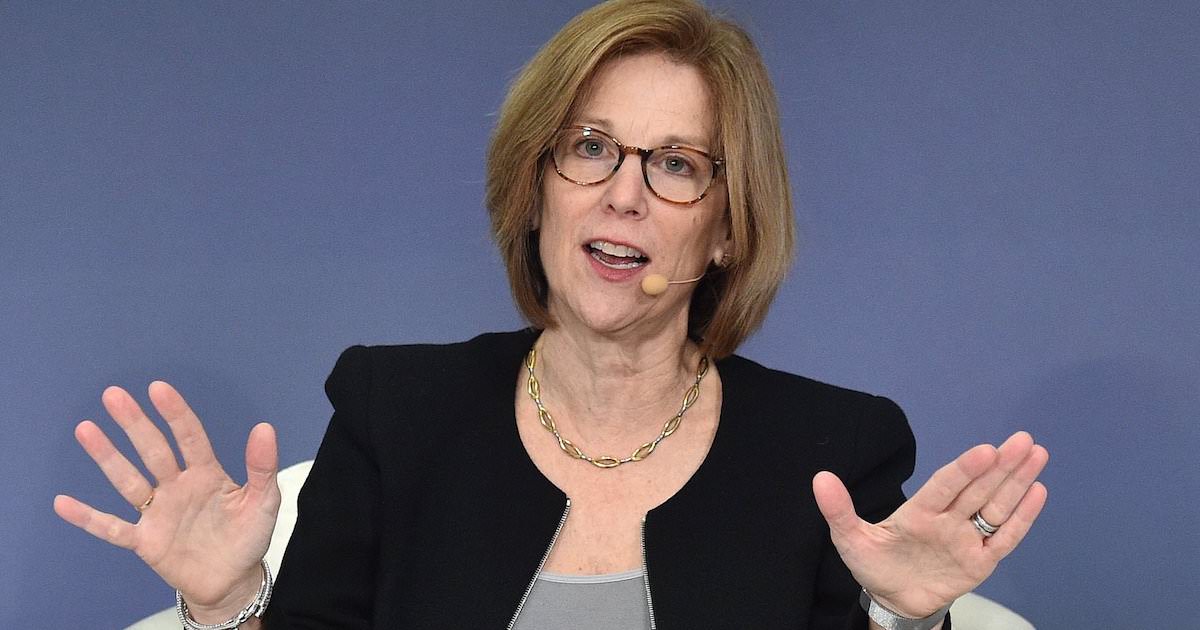
Chief Privacy Officer Jane Horvath to Leave Apple to Work at a Private Law Firm
Apple’s Chief Privacy Officer is about to leave the company to join a law firm that handled Apple’s legal tussle versus Epic Games.
State Privacy Legislation Getting Input from Tech Lobbyists to Push Weaker Protections
A report from “TNW” indicates that many state legislations concerning privacy are being written by tech lobbyists.
[U] DuckDuckGo Working with Microsoft Concerning Browser Privacy
A security expert recently revealed that DuckDuckGo’s browser allows for Microsoft trackers, despite the company’s hard stance on privacy.
Civil Liberties Group Warns of Global Privacy Breach, Google Largest Offender
A civil liberties group warns of a global privacy breach that auctions personal user data. Google is one of the largest offenders.
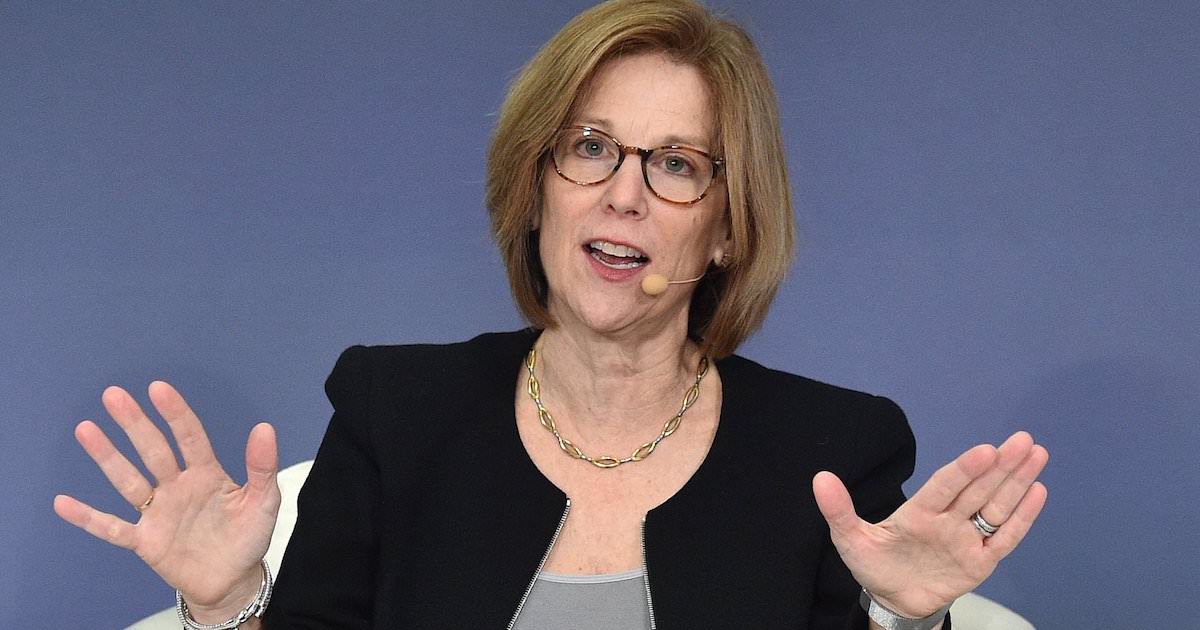
Apple Privacy Chief Jane Horvath to Chair Panel
Apple’s chief of global privacy, Jane Horvath, is scheduled to chair a panel at the annual Computers, Privacy & Data Protection Conference.
Facebook Unable To Account For Personal User Data: The Larger Problem Of Big Tech
Recent reports indicate that Facebook has little idea concerning how to handle personal user data. The report comes from a privacy engineer.
Apple's App Tracking Transparency Brings Losses to Other Tech Giants, Facebook Suffers the Most
A report by Lotame states that tech giants, especially Facebook, are set to lose revenue due to Apple’s App Tracking Transparency.
Tim Cook Argues Side-Loading Is Threat to Privacy Protections in Keynote Speech
During his keynote speech at a global summit, Apple CEO Tim Cook stressed the threat side-loading poses to privacy protections.
Ukrainian Developer MacPaw Develops Anti-Spyware Software in Fight Against Russia
Ukrainian developers MacPaw announces the release of its anti-spying app SpyBuster, a free download to help against the fight with Russia.
Apple and Google Find Backlash Over Support for Weak Privacy Laws
Lobbyists for Apple and Google are pushing for Utah’s privacy laws to become the norm across the U.S. However, critics feel they’re too weak.
Use Focus Mode to Make your iPhone a Gaming-Only Device
With Apple’s Focus Mode, iPhone users can create a custom, games-only profile, giving them peace of mind when a child plays with their phone.
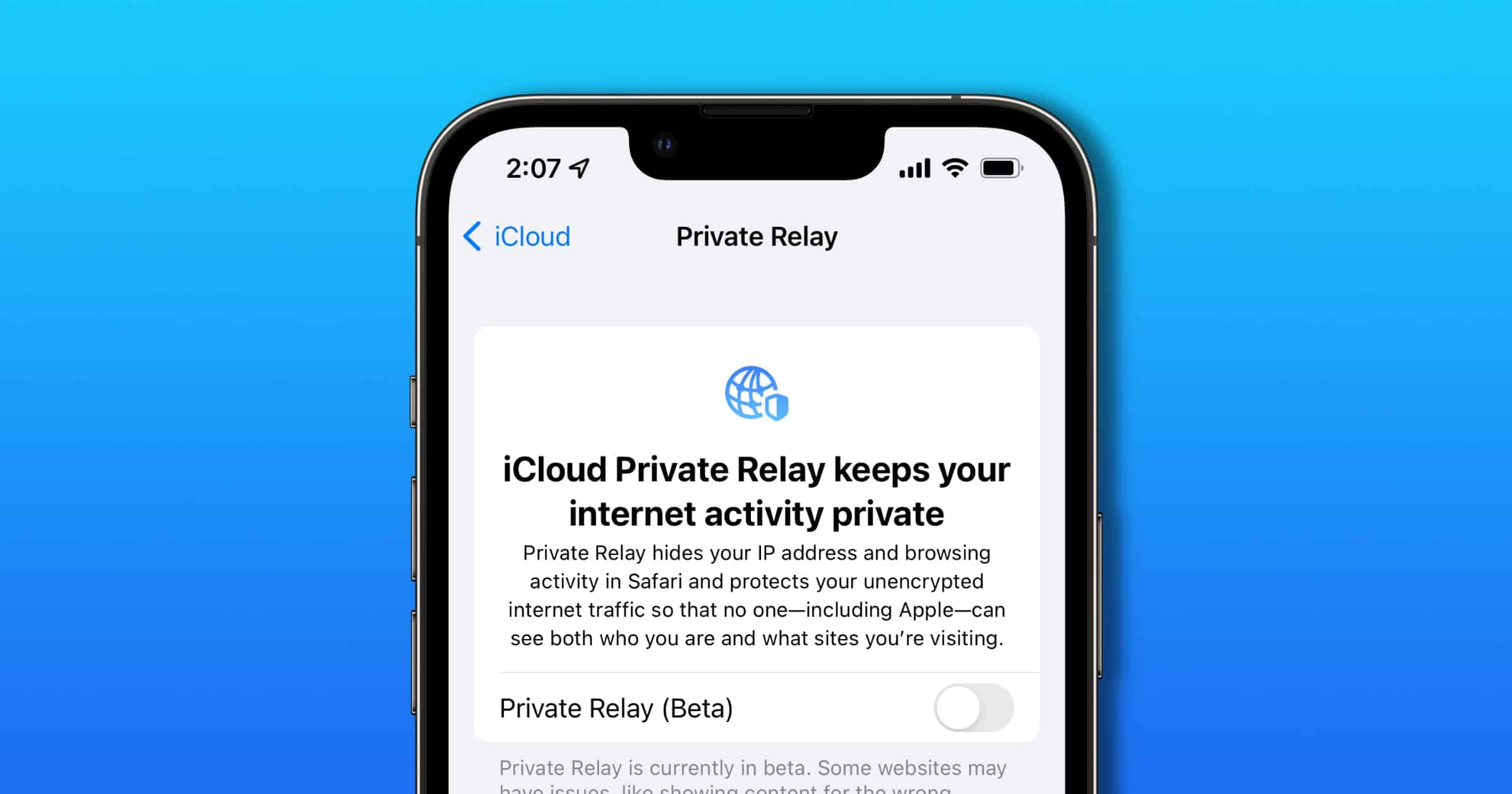
Cloudflare Explains how iCloud Private Relay Works
Have you ever wondered how iCloud Private Relay works? Cloudflare, a partner of Apple that operates portions of the infrastructure, explains.
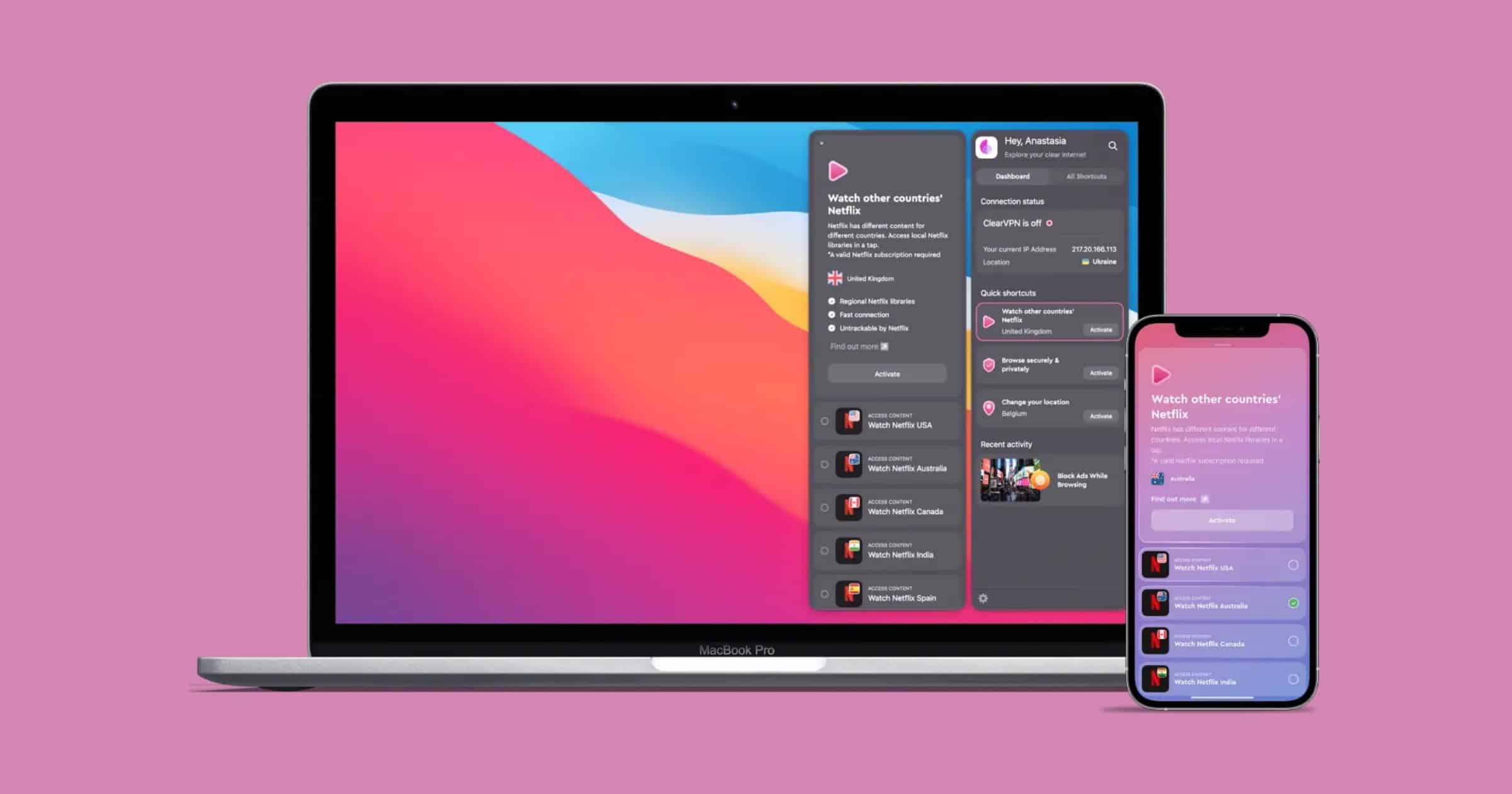
Here's How 'ClearVPN' From MacPaw Helps People Support Ukraine
ClearVPN from MacPaw, a company based in Kyiv, Ukraine, released a shortcut with information on trusted ways to support Ukraine.
Need Tor on iOS? 'Orbot' has Arrived on the Platform
Do you need Tor on iOS? Orbot, the official app from The Tor Project, has arrived to iOS to secure your network traffic.
New York Attorney General Warns of Malicious AirTag Tracking
New York Attorney General Letitia James issued a consumer alert to warn New Yorkers of malicious AirTag tracking.
Android Announces Ad Privacy Changes, Takes Swipe at Apple
Google announced an overhaul in its approach to advertising and privacy on Android phones, and got in a swipe at Apple.
Texas Sues Meta Over Facebook Facial Recognition
Texas Attorney General Ken Paxton filed a lawsuit against Meta. It seeks civil penalties due to Facebook’s facial recognition practices.






![[U] DuckDuckGo Working with Microsoft Concerning Browser Privacy](https://www.macobserver.com/wp-content/uploads/2022/05/DuckDuckGoMessyPrivacyMay2022Featured.jpg)